Just like other vital operations within a business, cybersecurity needs to have standardized procedures to follow. Policies like this can ensure that your organization is securing the data that is most vital to your operations.
Cybersecurity has come a long way since its inception in the 1970s. There are controls and standards that simply didn’t exist in the past. As the world continues to become increasingly reliant on technology not only in our personal lives but our professional lives as well. Just like other vital operations within a business, cybersecurity needs to have standardized procedures to follow. Policies like this can ensure that your organization is securing the data that is most vital to your operations.
A good security policy for an organization example would be an acceptable use policy. As one of many SANS policy templates, an acceptable use policy lays out a set of agreements for new employees to sign before gaining access to IT systems. There is no shortage of cybersecurity policy examples examples available for people to make use of. Provided below is a list of cybersecurity policies.
Acceptable Use Policy (AUP): Agreements settled on by a company to ensure each new employee uses technology and access to the systems appropriately.
Remote Access Policy: Remote work has really begun to take hold in the U.S. over the last few years. Outlining a policy to reduce the risk of attack due to unsecured networks.
Disaster Recovery Policy: Understanding the possibility of disaster and planning for ways to continue business throughout the fallout can be aided by this kind of policy.
Business Continuity Plan: Disaster Recovery Policies are often a part of a larger Business Continuity Plan (BCP). The idea is to continue business and security operations in the event of emergencies.
Data Breach Response Policy: This is a plan for handling a breach and reducing the effects on customers and operations.
There are plenty of information security policy examples PDF files available for download online. An effective example might be Bowie State University’s Sample Detailed Security Policy.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Types Of Security Policies
When it comes to cybersecurity, there are generally 3 categories that policies will fall under. The 3 types of information security policies are:
- Organizational Policies: Overarching policies that function as the foundation of security strategies.
- System-Specific Policies: Policies designed around proper use and protection of operationally vital systems.
- Issue-Specific Policies: Policies built around specific issues or risks that are most relevant to a business.
The list of information security policies in the previous section covers mostly either organizational policies or issue-specific policies. Organizational policies are policies that act as the outline for the entire security program. Many of the policies that fall under both the system-specific and issue-specific policy categories can be integrated into a greater organizational policy.
The National Institute of Standards and Technologies, or the NIST, offers a number of potentially useful policy templates that range from organizational policies all the way down to issue-specific policies. The NIST is a government entity that is responsible for creating a number of standards that IT companies are urged to follow for security compliance and regulations. NIST policies are often free for download and cover most of the current trends in cybersecurity.
Having a true understanding of the types of security policies you need and should implement into your business strategy is the first step towards a more complete security system. A CISO (Chief Information Security Officer) should be actively involved in the integration of a security policy into the larger business strategy. Companies like Trava offer virtual CISOs (vCISO) for small businesses that may not have a CISO in their ranks. Trava’s vCISOs specialize in optimizing security from the top down.
Cybersecurity Policy For Small Business
Small businesses take on their own set of challenges when considering cybersecurity policies. Small businesses are exceptionally susceptible to cyber attacks as they often don’t have the resources or staffing to focus on cybersecurity as much as they should. In 2021, small businesses were targeted for 43% of cyber attacks. This makes the implementation of an effective cybersecurity policy for small business extremely vital in today’s cyber landscape.
SANS templates are a great resource for small businesses looking to revamp their cybersecurity strategy. They offer a wide variety of policy templates so business owners can sample information security policy for small business operations. Understanding your business and its needs is the first step toward finding an appropriate cybersecurity policy template for small business use. Utilizing tools like risk assessments and vulnerability scanners can help identify where your current policy needs to be reworked.
Small businesses should also consider bringing on a CISO to keep an eye on the policy’s effectiveness and to troubleshoot in real-time. CISO salaries are often too much to budget for many small businesses. This is why vCISOs – as mentioned above – can be an effective and cost-efficient addition to a small business that handles large amounts of customer data. Instead of trying to make sense of cybersecurity policy example PDF files online, a vCISO will be able to help select the policy, or policies, that are right for your organization’s needs.
Staying on top of security takes a lot of attention to detail and constant education on the current trends of cybersecurity. For small businesses, it can often fall through the cracks. Security policies will usually build in regular training and checks to keep businesses accountable for their cyber awareness.
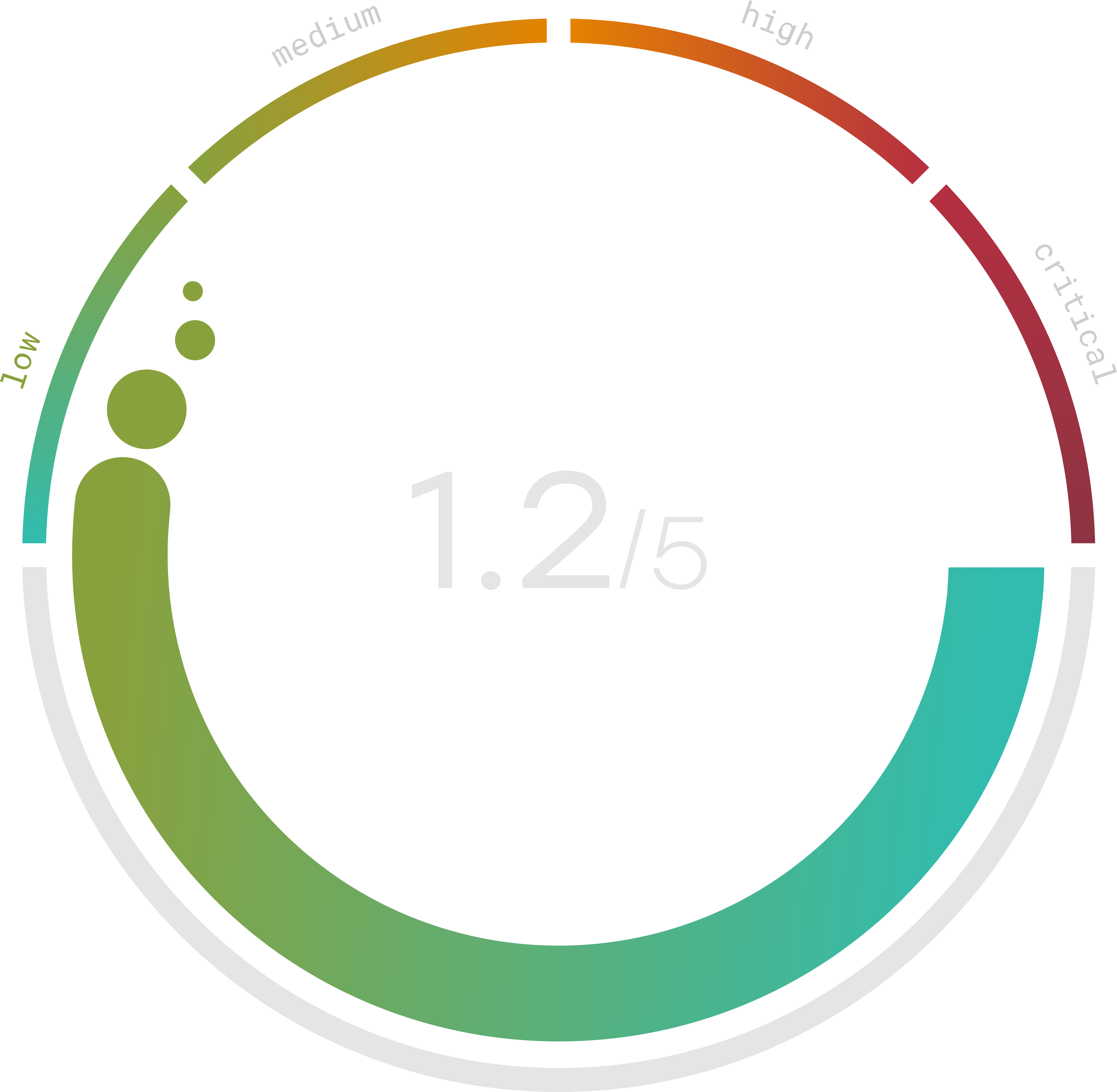
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Information Security Policies Examples
Information is the lifeblood of businesses. Handling that information safely is the challenge many businesses face, some without even knowing it. Hackers, natural disasters, and human error are all potential threats to consider when looking through information security policies examples. Again, information security policy PDF downloads are available on the SANS website and are excellent tools available to everyone.
The best way to protect your company is to get started right away. Many security companies and organizations, including SANS, offer an information security policy template for startups that can get a business strong footing in their cybersecurity from the beginning. Building a security policy into your business strategy from the start can give small businesses a considerable leg up in their security that can last as long as the business itself. It is crucial in 2022 to keep a watchful eye on security trends and best practices. A well-thought-out security policy is a great step in the right direction for startups.
While security policy templates can be simple enough to find, a single policy is often not enough to adequately protect a business. As mentioned earlier, there are 3 main types of security policies to consider when building a security strategy for the long run. For this reason, knowing your business needs and security weaknesses can help in assisting the decision and policy building process.
Protecting essential information requires building a plan and sticking to it. Policies lay out what a company can do to not only protect information but train staff on security protocols and help businesses hold themselves and their employees accountable. Cybersecurity is an organization-wide commitment. No single person or software can do enough to effectively secure all of the data a company handles on a daily basis.
Cybersecurity Policy Sample
There is no shortage of cybersecurity policy resources available to businesses these days. Between SANS and NIST, there are enough cybersecurity policy template examples for businesses to use for free. Selecting the correct combination of these templates is the part of the process that requires a bit of knowledge. Many times, small business owners are excellent at what they do. Cybersecurity likely isn’t what they do, making decisions like these seem overwhelming and tedious.
The cybersecurity policy PDF linked above can look like a foreign language to most people. Filled with technical jargon and security terms, it is not a field of knowledge that many owners will have a solid understanding of. For this reason, getting some outside help is nothing to be ashamed of. In fact, it is highly encouraged in 2022. When a company handles sensitive data, adhering to cybersecurity regulations can help improve the value of the business in the eyes of customers and potential partner companies. Compliance certifications often require specific policies to be implemented and honored. There is quite a bit that goes into these compliance regulations, but following specific policy guidelines is essential to virtually all of them.
It can be helpful to look deeply into each cybersecurity policy sample you find to determine the right path your business should take. They all offer something different, and depending on the systems used and the risks a business faces, the combination of policies is unique to each organization. Without some kind of information on what your business needs specifically, this can be a difficult task.
This is where companies like Trava come into play. Trava offers every tool you’ll need to assess and test your security so that you can pinpoint exactly what type of policies might work best for you. In addition, Trava’s vCISOs can help provide valuable insights on selecting and building security policies, meeting compliance regulations, and help organize employee security training. Contact Trava today to schedule a demo.
