A detailed cybersecurity policy can help companies protect their data and employees from cyber attacks.
Today, it may seem like common sense to monitor your online presence to prevent the exposure of private information to people with unscrupulous intentions. Even though there are a lot of advantages that come with internet access, there are risks as well—one of which is cyber. Cybersecurity refers to the practice of taking care of someone’s digital activities to make sure they are not going to surrender data to hackers or criminals. A detailed cybersecurity policy can help companies protect their data and employees from cyber attacks.
When it comes to formulating a cybersecurity policy, free cybersecurity policy templates abound. A cybersecurity policy for small business is going to include things like personal and company device security, email guidelines, data transfer guides, and more. A cybersecurity policy is going to set standards for your company’s approach to data encryption, protection, the use of social media, and information regarding how people can access the company’s information remotely if they are working from home or traveling. It is important to note that the main goal of the list of cybersecurity policies is to prevent cyber attacks and data breaches from taking down the company or exposing confidential information.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Information Security Policy for Businesses
All companies should have a cybersecurity policy. When developing an IT security policy, many businesses leverage a data security policy template. This template usually includes a framework for the information security policy itself, such as a list of information security policies, procedures, and standards. It can also be helpful to reference a cybersecurity plan template or security policy examples as you develop your information security policy.
Some of the most important components of a sample cybersecurity policy for small business include:
- Purpose: The purpose of the policy should clearly be stated. For example, the policy itself might state that the goal is to maintain the reputation of the business, prevent breaches of the network, and respect the rights of the employees and the customers.
- Audience: When looking at a small business cybersecurity plan template, the policy should also state who the audience is. This might include the customers, the staff, or the managers of the business itself. There might be a separate policy for executives.
- Information Security Objectives: A policy involving cybersecurity for small business should also clearly state the objectives of the policy. This should include the main objectives of information security which are confidentiality, integrity, and availability. Only individuals with the right authorization should have access to the data, and nobody should have access to the data unless they need it.
- Access Control: Next on the small business cybersecurity checklist is access control. It should list the hierarchy when it comes to deciding who has access to what information and how the information is going to be used. If someone needs access to something, it should let the employee know whom they should ask for help.
- Data Classification: Your policy for cybersecurity should also include how data is labeled, ranging from “secret” to “public” and everything in between. This is important for guarding against the cybersecurity threats for small businesses.
- Security Awareness and Behavior: When looking at an information security policy template, the policy should be one of continuing education. Everyone should be required to attend continuing education per this policy to ensure they stay up to date on the latest changes in the world of cybersecurity.
- Data Support: Also included in the information security policy for small business, if someone is having issues with their machine, equipment, or credentials, where should they go?
- Responsibilities and Duties: Finally, the cybersecurity policies and standards should also list out the responsibilities of the users when it comes to cybersecurity. They should be responsible for making sure they do not leave data lying around or expose their credentials where someone might be able to steal information.
These are a few of the key pieces of information that a company security policy and procedures document should cover. By making this information easily accessible, employees will be able to stay up to date on the latest security policies, while also understanding their roles in keeping the data of the company and its customers safe from harm.
Cybersecurity Strategy
When it comes to developing a cybersecurity strategy, it is critical to stay up to date on the best practices and trends. When referring to a cybersecurity strategy PDF or a cybersecurity strategy template, common components include:
- Have an Incident Response Plan in Place: One of the most important parts of a cybersecurity strategy action plan—if something happens, what does a response to the issue entail? If someone notices that something has happened with the network, whom should they call for help? What should they do with their information? There has to be a plan in place that should involve guidelines, priorities, fixes, and the overall response of the company.
- Continuing Education: One of the most important parts of a cybersecurity strategy example involves continuing education. Just as technology has changed the way businesses run, criminals are working to find ways around the latest cybersecurity measures; therefore, companies need to make sure that they educate their employees on a regular basis regarding how they can keep themselves and their information safe from harm.
- Resource Management: Another key part of information security policy examples is resource management. It is important for businesses to list out in their cybersecurity strategy how their resources are going to be used, when their equipment is going to be updated, and what their acceptable use policies are going to be. Having these measures in place can prevent cyberattacks from taking place, which is always better than trying to respond to one that has already happened.
These are just a few of the components that go into creating a strong cybersecurity strategy. All businesses need to think carefully about how they are going to develop a comprehensive cybersecurity strategy that can keep their employees, their customers, and their data safe from harm. When everyone works together to build and maintain a comprehensive cybersecurity strategy, businesses can reduce their chances of being impacted by cyber attacks.
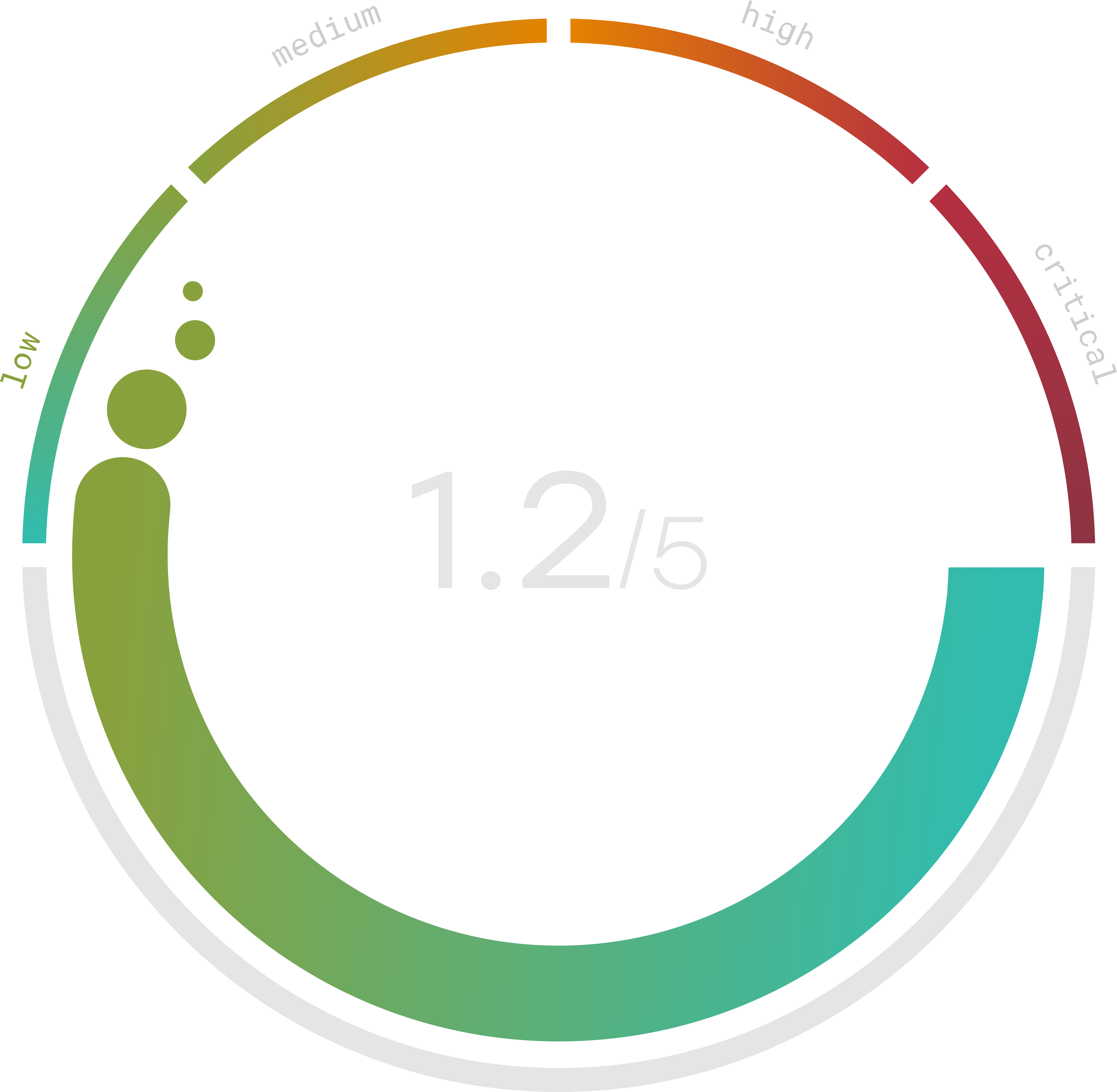
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
National Cybersecurity Policy
The National Cyber Security Policy is a framework for how the government protects its assets from harm. The U.S. cybersecurity strategy funnels down to the DHS cybersecurity strategy as well as the DoD cyber strategy.
There are several major components that all play a role in the national cybersecurity strategy. They include:
- Creating an ecosystem that is secure
- Setting up a framework that promotes an atmosphere of assurance
- Trying to encourage open standards whenever possible
- Setting up the protection and resilience of numerous areas of critical information infrastructure
- Reducing risks that are present in the data supply chain as information flows from place to place
- Setting up a partnership between the public and the private sector
- Educating others to be aware of the risks that come from cyber attacks.
United States cybersecurity laws have also been set up to try to reduce the chances that someone might be able to hack the United States’s networks and steal information. Even though the United States has been targeted by criminals in the past, a comprehensive strategy involving some of the latest cybersecurity measures can go a long way toward keeping the government’s data safe. As a result, this framework can be applied to almost any business that is looking to learn more about how they can set up a network that will protect their own assets from harm.
Cybersecurity Policy Jobs
Demand for cybersecurity policy jobs is high. As a result, over the past several years, cybersecurity policy job salaries have increased. When looking at a cybersecurity management and policy job description, it’s easy to see most require a degree in IT, computer science, or computer engineering. Often, cybersecurity analysts will gain policy experience elsewhere before they move into a dedicated cybersecurity policy role or department. Some of the biggest companies are posting job openings in their cybersecurity policy departments, providing everyone with the chance to read a cybersecurity policy analyst job description. Job sites like Indeed are full of postings—take a look at a cybersecurity policy analyst salary and job description to learn more about common requirements. For those interested in government work, USAJobs can help you find opportunities in this field.
Even though cybersecurity policy jobs are competitive, there is a lot of demand for individuals with these skills. It is always better to prevent these attacks from happening than to fix an attack that is already underway, which is why cybersecurity policy jobs are always in high demand.
