The Health Insurance Probability and Accountability Act (HIPAA) Security Rule is a federal law enacted in order to standardize the way sensitive patient health information was protected. Part of this security requires companies to utilize a HIPAA risk assessment to comply with the parameters of the act.
Patient health data can be extremely sensitive, so it is imperative for companies in possession of this information to do everything required of them to protect it. The HIPAA Security Rule is the way the government sought to protect that information. In response, many security entities have built a security risk assessment tool to help businesses understand where their security is most vulnerable.
Understanding the weaknesses of a security system is the first step in protecting patient data. In order to comply with HIPAA standards, a general risk assessment won’t necessarily be enough. HIPAA standards are more specific and patient-based than other security standards. Patient health data can literally be a matter of life or death, so more strict measures are expected.
HIPAA Risk Analysis vs Risk Assessment
A key term to keep in mind while understanding the difference between HIPAA risk analysis and a more general risk assessment. This term is protected health information (PHI). PHI is the core of the difference between the two.
For HIPAA compliance, a risk analysis is required. The HIPAA Security Rule defines a risk analysis as an “accurate and thorough assessment of potential risks and vulnerabilities to the confidentiality, integrity and availability” of PHI. A risk assessment is something that is a determination of the extent of which risk has affected PHI. It allows governing bodies to evaluate the damage done to the information, and informs them of whether or not a breach notification needs to be sent out to affected individuals. This is why a more general security risk assessment template may not be enough to satisfy HIPAA standards.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
HIPAA Risk Assessment Requirements
HIPAA risk assessments have a unique set of requirements that set it apart from other risk assessments. Considering that it is specifically geared towards PHI, the requirements aim more specifically at patient information. While they are altered to fit the idea of PHI, the general requirements are borrowed from the National Institute of Standards and Technology (NIST). These requirements are:
Identify technical and non-technical vulnerabilities that, whether accidentally triggered or intentionally exploited, could result in the unauthorized disclosure of ePHI (electronic Protected Health Information).
Identify natural, human, and environmental threats that could impact the confidentiality, integrity, and availability of ePHI.
Calculate the impact on the confidentiality, integrity, and availability of ePHI if a vulnerability is triggered or exploited, or if a threat manifests.
The HIPAA risk assessment requirements are designed with patient health records in mind. It is important to remember that there really is not a one-size-fits all risk assessment example. The connection to the NIST requirements cannot be understated.
The NIST has a HIPAA risk assessment tool available to health institutes or any other company that handles patient information. Finding a HIPAA framework PDF online may help in doing a little research to understand how it can apply to your specific business, but there is no prebuilt framework that will work for your own specific needs. It can be important to look into what other organizations are doing, and incorporate some of those aspects into your security strategy.
The risk assessment is made to determine the severity of risks posed to PHI. It concerns the impact of a potential breach via different entry points and risk paths within the security systems. It is recommended by HIPAA that these risk assessments be completed annually as a way to keep up with the ever-changing cyber security landscape.
HIPAA Compliance Requirements
HIPAA compliance requirements are laid out to offer organizations guidelines to adequately adhere to the measures of the law. Making sure your organization is compliant means following and upkeeping the guidelines and meeting all of the requirements at regularly requested intervals. HIPAA penalties can be costly and detrimental to patient wellbeing. Complying with the requirements will not only help you avoid fees, but help protect sensitive patient information. HIPAA compliance examples include:
- Privacy
- Security
- Enforcement
- Breach Notifications
- Omnibus
These five criterion focus on giving the organizations a roadmap to prepare for and handle potential breaches.
Privacy
Privacy refers to the patients’ rights to their information and the duty the organization has to protect that information in regards to holding and transmitting that information to appropriate entities. Medical information often has to be shared between medical care facilities to ensure the consistency of care. Protecting this information while it changes hands is one of the main functions of the HIPAA Security Rule.
Security
HIPAA defines security as the actions taken to protect the PHI adequately. This is often segmented into three main categories of security. The administrative duties of security refer to the administration’s part in the overall protection of health information. Then, there is the physical security of the assets involved in holding the PHI. Finally, there is the technical security involving the encryption of data and multi-factor authentication.
Enforcement
An often overlooked member of the HIPAA security examples, enforcement deals with the investigation into risk and potential breaches. The investigation of these attacks is important because an organization can mitigate the damage done to them by conducting prompt and thorough investigations. The faster an organization can find the entry point and what was compromised, the faster the recovery process can begin.
Breach Notifications
One of the toughest parts of a HIPAA risk management plan is the breach notification aspect. No one wants to tell their patients that their private information has been compromised. But it is a necessary step. It is important that companies remain transparent when sensitive information is attacked. It is a requirement that patients know their information has been compromised so that they can take the necessary steps on their side of things.
Omnibus
This aspect of the HIPAA compliance regulations that extends to business associates and covered entities is the Omnibus rule. Covered entities include contractors and other third parties that have a role in maintaining and holding patient information. This rule just means that they are responsible for adhering to HIPAA regulations just as much as the organization they do business with. These entities also need to make full use of HIPAA risk assessment services.
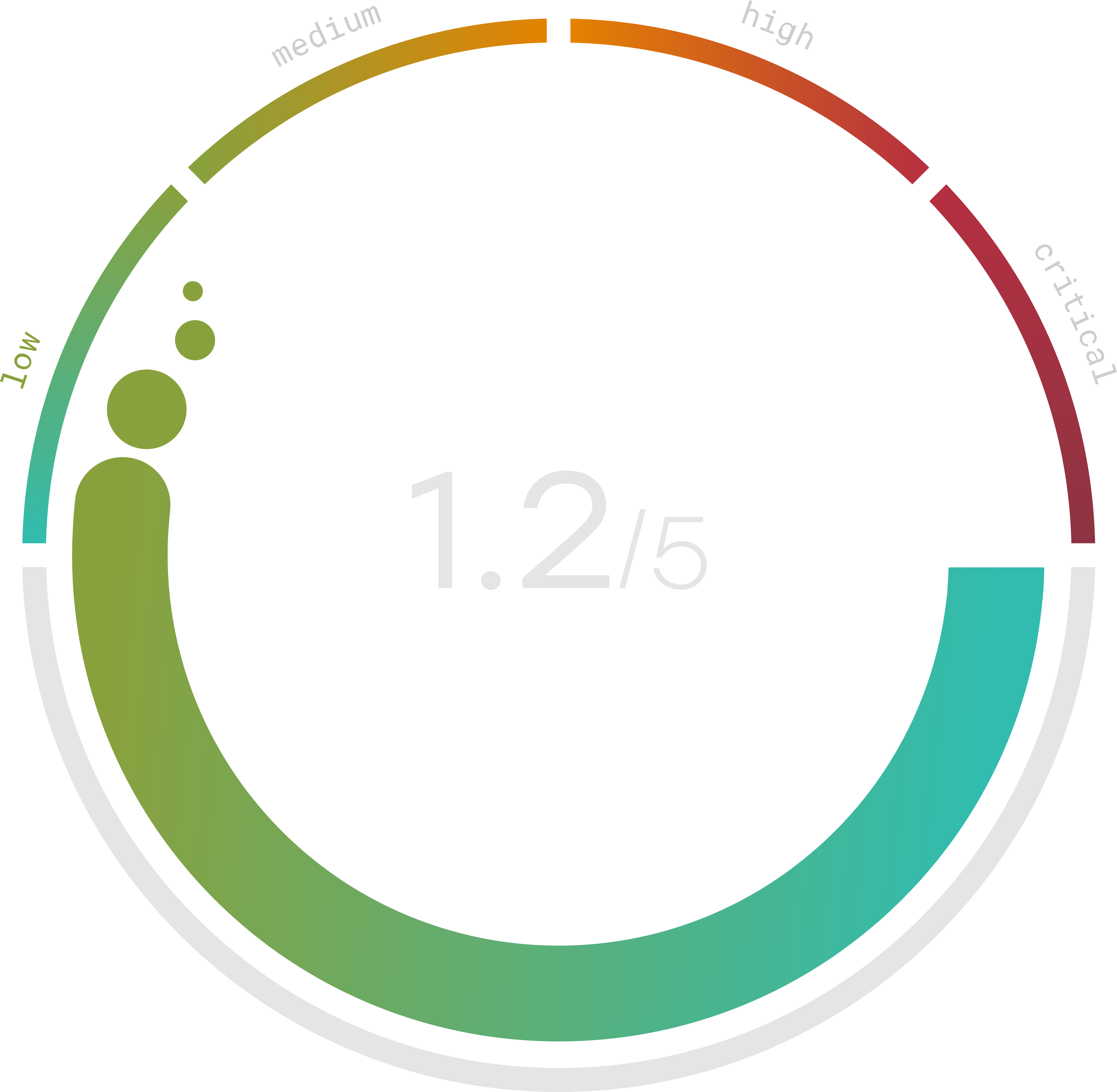
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
HIPAA Risk Assessment Checklist
Following HIPAA compliance regulations is not a cookie cutter process. Each organization needs to understand their own strengths and weaknesses to ensure they are up to standards with each of the requirements involved in meeting HIPAA compliance. There are, however, HIPAA risk assessment checklist examples all over the internet to help guide organizations to building their own templates. A risk assessment audit is one of the most surefire ways to test your security and determine whether or not it meets the requirements involved in HIPAA compliance.
A HIPAA audit checklist will look similar to the risk assessment checklist with the difference coming in a shift in language. Auditors will be looking to see if checklist items are met, rather than prompting the inclusion of certain measures. Consider downloading a HIPAA compliance checklist PDF to get the most accurate scope of the security measures needed to pass an audit. From there, you can build an easy to use HIPAA compliance checklist XLS (Excel Spreadsheet) for your staff to use in preparation.
HIPAA Risk Assessment Template
As stated above, there is no one-size-fits-all HIPAA risk assessment template. This doesn’t mean they can’t still be useful. Beyond that, there are HIPAA tests that can be used to familiarize your staff and yourself with the finer points of HIPAA regulations. HIPAA assessment answers will simply be the correct ways to disclose, transmit, and store PHI. Testing your essential staff will create a baseline of knowledge for HIPAA and the regulations built in.
Security risk assessment (SRA) tools can be used to help you understand where your security is lacking and can offer risk assessment templates. A HIPAA SRA tool is available on the Health IT government website. There are more SRA tools than just this one, but being a tools specifically built for HIPAA risk assessments, it is a great place to start.
The government entity, Health and Human Services, offers a detailed HIPAA compliance PDF free to download for any health organization looking to get their audit process started. It covers everything from basic HIPAA information to the finer points of HIPAA compliance. Without a well-rounded understanding of HIPAA itself, meeting regulatory requirements is virtually impossible.
With this knowledge you can start to build a risk assessment template that works for your organization. From there, you can start to look for a powerful tool that will best fit your needs and help you comply with the HIPAA regulations.
Trava offers one of the best risk assessment tools for HIPAA compliance. Trava’s risk assessment tool will not only tell you where you are vulnerable to attack, but give you detailed reports and actionable strategies for remedying the issues. Contact Trava today to schedule a demo and get one step closer to HIPAA compliance.
