This article was updated November 2024.
If you take your cybersecurity seriously, you’ve likely already heard a little about SOC 2 compliance. But what is SOC 2 compliance in the first place? What does SOC 2 stand for? There are a lot of questions surrounding SOC 2 and its functions in your business. We will explore the entirety of SOC compliance and give you the information you need to optimize your cybersecurity and keep up-to-date on SOC standards.
There’s no better place to start than to define the meaning of SOC 2. SOC stands for System and Organization Controls. This is a compliance standard for service organizations put forth by the American Institute of Certified Public Accountants (AICPA) based on the Trust Services Criteria (TSC). The criteria include security, availability, processing integrity, confidentiality, and privacy. There are three types of SOC reports, but SOC 2 is the one to look at when dealing with cybersecurity, as it is often referred to by customers when evaluating a company’s overall security.
Now that we have a basic understanding of what a SOC 2 report looks at and who might be interested in the results, we can look at what it might take to prepare for a SOC 2 audit. It is important to note that failing a SOC 2 audit will not shut your business down. It simply means your company is not as secure as you might have thought it was.
The most effective ways to get your business ready include creating up-to-date administrative policies, setting technical security controls, and gathering documentation and evidence for a reputable firm to examine. By updating standard operating procedures in system access, disaster recovery, and security training and roles, an auditor will have less to flag in his report giving your business a better chance of getting certified.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
SOC 2 Compliance Requirements
The AICPA defines five Trust Services Criteria your business needs to verify during a SOC 2 audit to attain the compliance credential. The compliance requirements are considered rough guidelines rather than strict rules. The way each company opts to implement these guidelines differs depending on the business type and industry.
However, security is considered the only common requirement that’s mandatory for compliance, while the remaining four are largely optional. Each one of the five compliance categories focuses on a specific security requirement.
Security
You must be able to show that all data and information systems in your organization are sufficiently protected against anything that could damage their integrity. This includes protection from unauthorized access, damage and loss, compromised availability or confidentiality, and unauthorized processing of user data.
As the baseline for every SOC 2 framework, the security requirement encompasses everything from endpoint security and firewall configurations to risk management, organizational structuring, and user security awareness. A base level of security is required for the user throughout its lifecycle, from creation to deletion or archiving.
Availability
Data and services availability refers to a user’s ability to access company services and products, as agreed upon in the terms of service. SOC 2 compliance doesn’t have a set minimal requirement for businesses to meet. However, an audit can verify the implementation of performance monitoring and disaster recovery measurements that could minimize unplanned downtime.
Confidentiality
Any data or personal information a user provides your business is done under the assumption of confidentiality. Confidential user information includes everything from their contact information and IP address to financial information.
Following the SOC 2 framework, you’re responsible for maintaining the confidentiality of user data at all times. This includes not sharing it with business partners without explicit consent, strong encryption, and implementing strict access control policies throughout the company’s hierarchy.
Privacy
The privacy criterion protects all personally identifiable information (PII) from misuse, unauthorized access and processing, and loss. It covers data in all its stages, including collection, use, storage, and deletion. While there’s a lot of overlap between privacy, security, and confidentiality, privacy only applies to PII, whereas confidentiality and security are concerned with all user data.
Processing Integrity
Processing integrity evaluates the quality of data processing done on user data. The goal is to ensure that the system processing of data is complete, accurate, and valid, and has been authorized by the user.
It also focuses on the overall performance of data processing, examining factors such as data processing timing, process reporting, and system logging.
What Is a SOC Compliance Checklist?
Working with a checklist is one of the best ways you can ensure that your business is ready for a SOC 2 compliance audit. Which steps you choose to implement depends on the scope of your report and whether you’re planning on going beyond the universal security requirement.
A SOC 2 compliance checklist lists the steps — some universal, some unique to your organization — your team must take to do well in an audit. Here are five of the most common tasks to help you get started:
1. Determine the Type and Scope of the Audit
Whether you’re seeking Type 1 or Type 2 SOC compliance will influence the preparations needed before an audit. Also, consider the scope of the test and whether it’s going to cover a few of your systems and services or the entirety of your infrastructure.
2. Select Your Trust Services Criteria
While the security criterion is the only one that’s mandatory for a SOC 2 compliance certification, you may choose to validate one or more of the remaining four requirements. If you’re short on time and resources, it’s best to stick to the requirements most relevant to your business.
3. Conduct an Initial Self-Assessment
A self-assessment can help identify risks already present in your infrastructure. This will give you the chance to implement any necessary changes to your internal operations before seeking the official SOC 2 certification.
4. Implement Continuous Monitoring
New issues can arise with the slightest update or change in your systems. That’s why it’s important to have a reliable monitoring system in place to ensure that the changes you implement are effective long-term.
5. Schedule a SOC 2 Audit
You can have the SOC 2 audit performed by any certified professional accountant (CPA) firm. However, it’s best to work with an independent CPA rather than one you’ve already been working with for accounting work.
What Is the Difference Between the NIST Framework and SOC 2?
Put in place by the U.S. Department of Commerce, the National Institute of Standards and Technology (NIST) cybersecurity framework is a set of guidelines to help organizations self-assess their systems’ risk of cyberattacks. It’s entirely voluntary and can be used by businesses of all sizes and industries.
In comparison, SOC 2 is an auditing protocol that focuses on user data kept by the business. Proving SOC 2 compliance assures customers and partners that your business has implemented sufficient controls to protect personal data and information.
SOC 2 Vs. ISO 27001
While a SOC 2 compliance certification is helpful in relaying to clients that your organization is secure and safe, it isn’t the only type of certification that can express this to potential customers. The International Organization for Standardization (ISO), in partnership with the International Electrotechnical Commission (IEC), published this standard for information security. When it stands alone, ISO 27001 is a framework for best practices in safeguarding data. Getting certified against ISO 27001 shows customers that your company takes the appropriate steps to secure their data.
It can be confusing when trying to determine who needs SOC 2 compliance and who needs ISO 27001 certification. Which type of certification best suits your business? While it is true that these both deal with similar security controls, the difference arises with the way the controls are practiced. Defining which certification best suits your needs, you must understand the slight differences between each.
ISO 27001 tends to focus on the implementation maintenance of an information security management system (ISMS). Essentially, they inspect the development and use of an overarching security framework that manages the data protection practices put in place by the company itself. Achieving ISO 27001 compliance means you must undergo a risk assessment, identify and implement security controls based on the results of the assessment, then regularly review the controls for effectiveness.
SOC 2 is a bit more fluid in the way a company can go about its certification, but not at the expense of overall security. With the use of the TSCs discussed above, a company can choose to implement as many or as few controls on them as they see fit. Only security controls are required for certification. Do remember, the AICPA SOC 2 is more flexible than the ISO 27001, but not at the expense of general security.
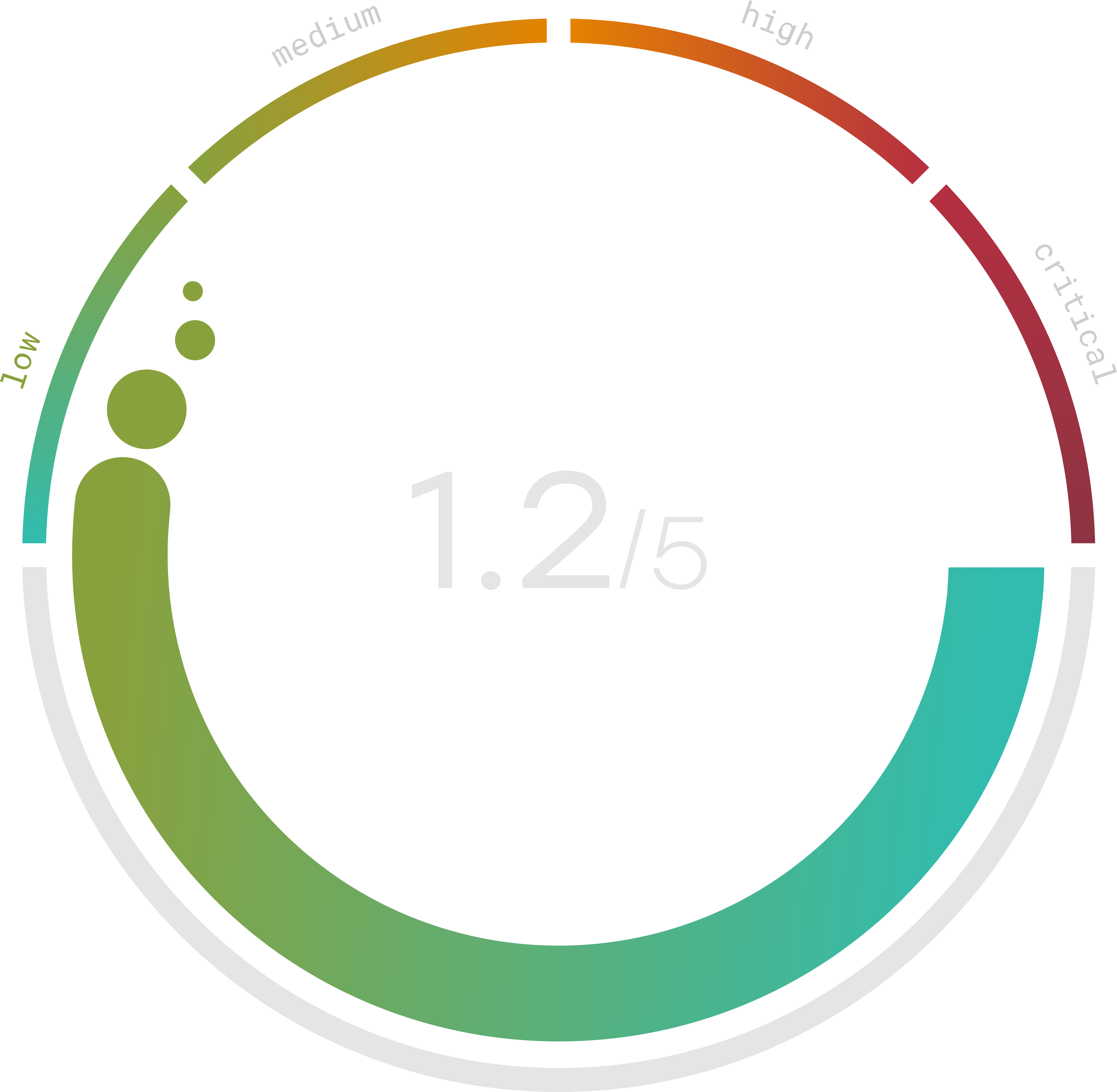
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
SOC 2 Type 2
If you’ve decided that the SOC 2 compliance is the right fit for your business, then it will be important to understand the different types of reports that come with it. Understanding the different types of reports will give a little more insight into SOC 2 compliance, meaning things like the SOC 2 controls list, SOC 2 Type 2 cost, and more. It is vital to understand which report your company will benefit from so you don’t waste precious time or money on unnecessary certifications.
Before diving into the other SOC certifications that exist, we need to understand the two “types” of reports. Type 1 reports offer insight into the design of security controls at a single point in time. Type 2 reports look at the operating effectiveness of security controls over a set period of time. While they take longer, they are widely viewed as a more accurate representation of an organization’s security.
SOC 1 certifications deal mostly with internal controls over financial reporting. It caters to organizations that process financial transactions and related data for their clients. They can be important for companies dealing with high volumes of financial transactions, but don’t look any deeper than that. The SOC 1 Type 2 report is the only report that holds any water in the sense of reliability in financial security. SOC 1 certification cost can range between $10K and $20K.
SOC 2 Type 2 reports are viewed as the most important when it comes to credibility in the eyes of your clients. They show a comprehensive report of how well a company commits to protecting customer data over a period of time. SOC 3 compliance is similar to SOC 2 but much less detailed and not as trusted as the SOC 2 certifications. SOC 2 Type 2 cost will usually range from $30K to $60K for the audits alone.
