Did you know that 1 million passwords are stolen weekly, and 81% of all breaches leverage stolen or weak passwords? Scary stuff.
Multifactor authentication (MFA) can protect you even if your password is compromised. It requires users to verify their identity using more than their username and password. So, when (not if) malicious actors steal your password and username, they can’t access your data without the additional authentication factors required by MFA.
In this article, we look at the examples of MFA to help you understand how you can implement it in various contexts to provide a robust defense against unauthorized access.
Authentication factors
You must understand the authentication factors to grasp the concept of MFA fully. This is because MFA works by combining various authentication factors to verify a user’s identity before granting them access.
The three authentication factors are knowledge, possession, and inherence.
Knowledge factor
The knowledge factor requires you to identify yourself through something only you know, such as a password or PIN, in addition to your email, username, or other identifying information. It is the most common authentication factor.
Knowledge authentication factors include:
- Passwords
- Security questions
- Personal identification numbers (PINs)
The knowledge authentication factor method is secure only if the information remains secret. Some passwords, PINs, and security questions can be cracked using brute-force methods.
Possession factor
This authentication factor requires you to identify yourself through something you possess, such as a mobile phone or security token, in addition to your email, username, or other identifying information.
Here are a few examples of possession authentication factors:
- Security token
- Mobile device
- Smart device, or
- USB key
Inherence factor
Inherence MFA authentication factor requires you to identify yourself by providing information inherent to you, such as your fingerprints, in addition to other identifying information. Here are a few examples of inherent authentication factors:
- Fingerprint scans
- Retina scans
- Facial recognition
- Voice recognition
Understanding these authentication factors and how they combine to form the different authentication methods is crucial for implementing secure access control systems.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Types of authentications
There are three types of authentications: single-factor (1FA), two-factor (2FA), and three-factor (3FA). Their difference lies in the number of authentication factors you need.
Single-factor authentication
1FA requires users to provide only one piece of verifiable information to authenticate. Most 1FA systems require passwords, PINs, and other knowledge factors, but they can also work with possession or inherent factors, such as fingerprints.
Two-factor authentication
2FA is a type of MFA that requires users to provide two pieces of verifiable information to authenticate. The second piece of information helps maintain security if the first is compromised.
The two pieces of information must be from different authentication factors. For example, something they know (password) and something they are (fingerprint), or something they know (username and password) and something they have (mobile phone).
The most common forms of two-factor authentication include:
- Text message: A code is sent to the user’s mobile phone via text, which they must enter to complete the login process.
- Authenticator apps: The apps generate time-based one-time codes for login.
- Email verification: A code is sent to the user’s email address, which they need to enter to authenticate.
- Phone call: Users receive the code via phone call, which they need to enter to authenticate.
Three-factor authentication
With 3FA, users must provide more than two credentials from different authentication factors. For example, a user trying to access a system using 3FA will have to provide something they know (username and password), something they have (fob or phone), and something they are (fingerprint or retina scan).
Multifactor authentication is more secure than single-factor authentication. An attacker with a single attack skill can compromise a system with just one authentication factor. But if it uses more than one factor, the attacker needs multiple attack skills and must wage multiple attacks simultaneously to succeed. It’s too complicated.
Examples of MFA methods
Here are examples of MFA methods to help you bolster your online security and safeguard your digital identity.
Examples of two-factor authentication
2FA is the most widely adopted form of MFA as it enhances security without affecting the ease of use. It is implemented across various services and platforms, including email, banking, social media, etc.
Here are some common examples of 2FA methods
-
SMS and phone calls
After keying in your username and password, a system that uses SMS-based 2FA will send a code to your phone and ask you to enter it for authorization. The code arrives almost immediately and is time-sensitive. They can also call you and tell you the code.
It is pretty secure, as calls and text messages aren’t easy to intercept. However, it assumes only you have access to your mobile device. If someone manages to access your phone, the extra step won’t work to keep the system safe.
An excellent example of SMS or call-based 2FA is logging in to WhatsApp for the first time. You must enter the code sent to your mobile phone for authorization.
-
Security questions
Systems that use security questions 2FA ask you to create a username and password and answer a question only you can know. They can ask questions like, “What is the name of your first pet?” or “What’s your mother’s maiden name?”
After signing up, you must enter the password and answer your question to log in. The security question can also be used as a backup to verify you’re the owner if you lose your password.
The downside of security questions is they often relate to basic information about you, so they can be easily compromised.
-
Authenticator applications
Authenticator apps like Google Authenticator, Authy, or Microsoft Authenticator can generate time-sensitive one-time passcodes. You will use the code, along with your username or email and password, to verify your identity.
-
Email-based 2FA
Email-based 2FA works like SMS messages, but you don’t need a specific device to access them. The system sends a code to your email address, which you can access on any device. However, if you leave your email logged in or a hacker gains access to your email and password, your code can be compromised, giving the malicious actor unrestricted access to the system or account.
-
Push notifications
Push notifications work like SMS messages because you must have your phone to receive the notification. However, instead of a code, the notification lets you know someone is trying to access your device and has the option to allow or deny them access.
The notification often contains general details about the type and location of the device trying to access your account.
Examples of three-factor authentication
3FA involves a combination of three things: something a user knows, something a user has, and something the user is. It is much less common than 2FA because it is too costly to implement and can be cumbersome and challenging to use.
Additionally, 2FA suffices for many security risks. So, organizations don’t see a point in adding the complexity of 3FA and negatively affecting ease of use. As 3FA is uncommon, you might wonder, “What is an example of 3-factor authentication MFA?”
Here are a few:
-
Password + smartphone + fingerprint scan
Systems with this MFA require you to identify yourself using your username, password, a code they send to your phone, and your fingerprint. If a malicious actor compromises your password and has access to your phone, they still can’t access the system because your fingerprint is unique to you. The fingerprint requirement enhances your security posture.
-
Pin + hardware token + retinal scan
A system with this 3FA requires you to enter your PIN, use your token to generate a unique one-time code and scan your retina. Even if a hacker brute forces a weak PIN and physically steals the hardware token, they won’t be able to access your account or system.
A retinal scan is impossible to forge or replicate, so malicious actors can’t access your account or system, even if they have your PIN and token.
-
Password + smartphone app + voice recognition
A 2FA system that verifies your identity through a password and a code sent to your mobile phone can be effective as it verifies that you have control over your device. However, it’s not enough because hackers can compromise your password and gain access to your phone.
To ensure gaining access to the two doesn’t end in a compromised system or account, 3FA adds voice recognition verification. It is a robust way to verify your identity, as it is impossible to replicate the unique characteristics of someone’s voice.
-
Pin + smart card + handprint scan
To access a system or account with this 3FA method, you must enter your PIN, use a smart card as a possession factor to generate a one-time code, and scan your handprint.
Like the other 2FA methods, a malicious actor with your smart card and pin can’t access your account or system because your handprint scan is unique. No one can access it but you.
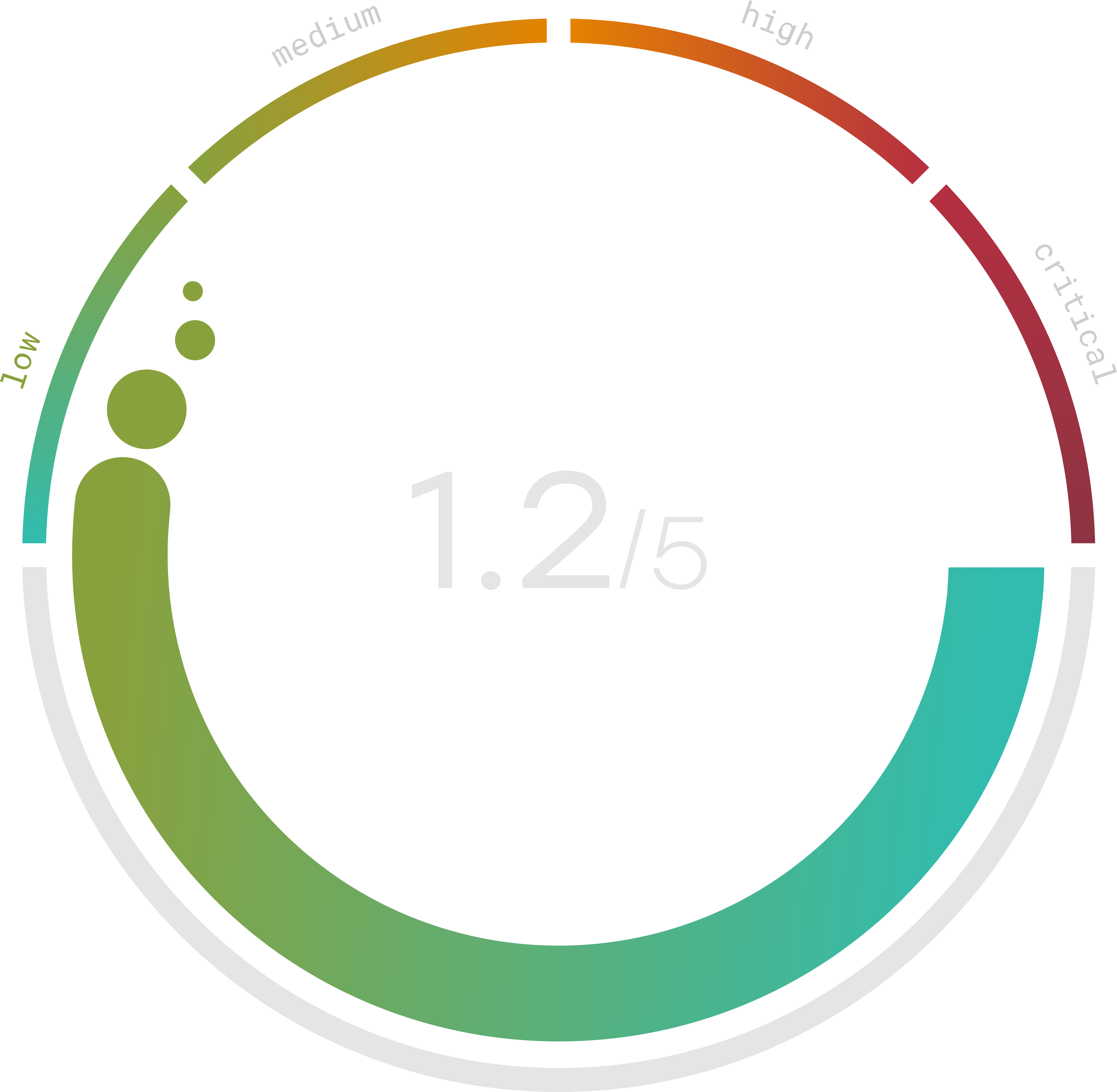
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Multifactor authentication with Google
Google is at the forefront of implementing and promoting MFA to enhance user account security across its suite of products and services.
The multifactor authentication Google uses to protect user data is 2FA. It allows users to link their Google accounts with their mobile devices. To access Google’s suite of services or products, you must input your email and password, then receive a push notification or a one-time verification code via SMS, call, or the Google Authenticator app for verification.
However, Google only offers 2FA. There is no 3-factor authentication Google. If you want stronger account security, you can enroll in Advanced Protection. Google recommends it for anyone at a higher risk of targeted online attacks, such as activists, IT admins, and journalists.
In Advanced Protection, the second verification step is not a push notification or a verification code. It is strictly a security key as it is more secure.
Some Google services like Google Play may ask you to verify your identity with a third factor, like your fingerprint or face scan. But the biometric data is only used locally on your phone and not sent to Google, so it doesn’t qualify as a 3FA.
If you want to use 3FA for your Google account, you may need to use a third-party service like Infobip. But they have some limitations. They may not be compatible with all Google services and devices and may require additional fees and permissions.
There’s also no three-factor authentication Facebook feature. Like Google, most social media platforms only use 2FA.
Multifactor authentication in cybersecurity
Multifactor authentication is a critical component of a robust cybersecurity strategy as it addresses the weaknesses of traditional 1FA.
MFA adds one or more authentication layers, eliminating the risk of unauthorized access inherent in 1FA systems. For example, if a cybercriminal obtains a user’s password through phishing, social engineering, brute force, etc., they would still need their phone, biometric data, or physical token to bypass the other authentication factors.
MFA in cybersecurity also serves as a tool for detecting and preventing unauthorized access. When a user fails to provide additional verification, the system can monitor their attempts for suspicious behavior.
For example, suppose a user typically uses a particular device to log in from a certain location. In that case, if a failed login attempt comes from a different device and location, the system can flag it as suspicious, request additional verification, and notify the user. This can help organizations identify and respond to cyber threats quicker and more effectively.
Additionally, many regulations and standards, including GDPR, HIPAA, and PCI DSS, recommend or require organizations to use MFA to enhance data protection. They acknowledge the critical role of MFA in reducing the risk of unauthorized access and protecting sensitive data.
What is an example of 3-factor authentication in cybersecurity
A common example of 3FA in cybersecurity involves a combination of something the user knows, something the user has, and something the user is.
- Password (knowledge factor): The user starts the authentication process by entering a password, which only they should know.
- Smartphone or hardware token (possession factor): The user receives a one-time code on their smartphone or generated by the hardware token, indicating their control over the device.
- Fingerprint scan (inherence factor): The user places their finger on a fingerprint scanner, and the system verifies their identity based on the unique patterns in their fingerprint.
The user must provide the correct password, possess the authenticated smartphone or hardware token, and authenticate their fingerprint to gain access. Even if an attacker compromised two factors, they would still need to bypass one more to gain access.
Implementing MFA for all your accounts can enhance your overall security. However, not all accounts need MFA security. To balance usability and security, only consider securing accounts that contain sensitive information. They include:
- Email accounts
- Financial and banking accounts
- Healthcare portal
- Cloud storage and file sharing
- Government and public services accounts
Two-factor authentication for cyber awareness
In the rapidly evolving digital landscape, 2FA is fundamental in enhancing cybersecurity awareness. It can help ensure users adopt additional security measures to protect their digital identities and sensitive data.
Some roles of 2FA as a cyber awareness tool include:
- Educating users: Implementing 2FA encourages users to understand the importance of safeguarding their online presence and data. It highlights the need for proactive security measures.
- Promoting responsible online behavior: Emphasizing the use of 2FA encourages individuals to adopt responsible online behavior. It can make them more cautious about potential threats and adhere to security best practices.
How to respond to identity theft
There are three things you should do if you suspect identity theft to minimize the damage:
- Immediately report: Report the incident to the appropriate authorities, such as your bank or credit card company, and file a complaint with your local law enforcement agency.
- Monitor your accounts: Regularly monitor your financial and online accounts for unauthorized or suspicious activities.
Update security measures: Change passwords and strengthen security by enabling 2FA to prevent further unauthorized access.
More multifactor authentication examples
MFA is a versatile approach to enhancing digital security, with several applications across industries. Here are some more MFA examples.
- Mobile-based authentication: Many applications and services send one-time passcodes to a user’s registered mobile number, which the user must enter with their password to gain access.
- Fingerprint scanning: Users must provide their fingerprints in addition to other credentials for authentication.
- Voice recognition: Verifies a user’s identity by analyzing their unique voice patterns.
- Smart cards with pins: Smart cards contain embedded chips that store authentication information. Users must possess the card and provide a PIN for access.
- Face recognition: Users must scan their faces for authentication.
These examples can help you understand how to implement MFA across different domains.
Multifactor authentication apps
MFA apps enhance the authentication process by simplifying the generation and access of the time-sensitive one-time passcodes needed when logging in.
These applications are pretty safe. They use robust encryption algorithms to protect the codes they generate to reduce the risk of interception. The codes are typically time-sensitive, with a short validity period (a few seconds or a minute). This small time window reduces the window of opportunity for attackers to misuse intercepted passcodes.
Each MFA app links to a specific device and generates the passcodes locally without communicating with the server, adding an extra security layer.
Apart from the added security, a benefit of using MFA applications is their convenience. You can quickly generate verification codes directly on your device, so you don’t need additional physical tokens.
Many MFA apps are free to use, providing a cost-effective way to implement enhanced security measures. They include:
- Google Authenticator: A widely used authenticator app by Google that generates time-based passcodes and supports multiple accounts.
- Authy: An authenticator app that offers encrypted backups, multi-device support, and a user-friendly interface.
- Microsoft Authenticator: Microsoft’s authenticator app provides additional security for Microsoft accounts and various third-party services.
These apps work seamlessly on various platforms. You can find an authenticator app for PC, apple authenticator app, and other platforms, enhancing accessibility and user experience.
MFA in various contexts
MFA is a versatile security measure that you can use in various contexts to provide a robust defense against unauthorized access. Some of its uses in various contexts are discussed below.
MFA in banking and finance
- Online banking: Banks implement MFA to secure online banking transactions. Customers often use a combination of passwords, SMS-based codes, or biometrics to authenticate their identity.
- Financial transactions: During financial transactions, MFA adds an extra layer of security, ensuring that only authorized individuals can initiate and approve transactions. The multiple forms of identification make it more challenging for unauthorized individuals to access financial accounts, conduct transactions, or perform sensitive actions.
MFA in healthcare
- Electronic health records (EHRs): Healthcare institutions employ MFA to protect electronic health records, ensuring that only authorized personnel can access and update patients’ medical information. It is a compliance requirement.
- Telemedicine: With the rise of telemedicine, MFA helps secure digital consultations and patient-doctor communications, maintaining the privacy and confidentiality of health-related discussions.
MFA in enterprise security
- Employee access: Enterprises use MFA to secure employee access to internal systems, applications, and databases, preventing unauthorized access to sensitive corporate information.
- Remote work security: With the increasing trend of remote work, MFA ensures secure access to company resources from various locations and devices.
MFA in government and public services
- Government portals: Government websites and portals often implement MFA to secure citizen data and maintain confidentiality during online interactions with government services.
- Identity verification: MFA is utilized for secure identity verification processes in public services, preventing identity theft and ensuring the authenticity of users.
MFA on mobile devices
Mobile devices have become integral to our lives, serving as powerful tools for communication, productivity, and accessing various online services. MFA on mobile devices is a crucial security measure that ensures secure and convenient access to sensitive information and accounts.
How MFA works on mobile devices:
- 2FA: Mobile devices are often used as a second factor in 2FA. Users receive a one-time passcode on their mobiles, adding an extra layer of security beyond passwords.
- Biometric authentication: Mobile devices often incorporate biometric factors like fingerprint scanning or facial recognition for authentication, providing a secure and user-friendly MFA option.
- Authentication apps: Authenticator apps, installed on mobile devices, generate time-based codes, serving as an additional authentication factor for various online services.
MFA devices for mobile
Some devices you can use for MFA include:
- Smartphones: The primary device for MFA, where users can receive authentication codes via SMS, use authenticator apps, or leverage biometric authentication.
- Wearable devices: Smartwatches and fitness trackers can act as MFA devices, providing secure authentication codes and alerts directly to the wearer’s wrist.
Conclusion
Malicious actors can obtain your password through so many techniques, including phishing, keylogging, and brute force attacks, that it’s impossible to be sure they don’t have it yet.
The only way to deny them access, even if they have your password, is to secure your accounts with MFA. It requires at least two forms of authentication before granting anyone access to your accounts, significantly reducing the risk of unauthorized access.
The examples of MFA discussed above illustrate the different ways to implement it in various contexts to safeguard your digital identity and sensitive data in an increasingly connected and digital world.
