Vulnerability scanning generally aims to identify and potentially remedy vulnerabilities in computer systems, but there are many types of vulnerability scanning. One type of vulnerability scanning is network vulnerability scanning, which is used to scan and assess the security of the network infrastructure, including switches, routers, and firewalls.
Another type is host-based vulnerability scanning–which is used to scan individual devices, such as servers, network devices, and workstations for security vulnerabilities. A host-based scanner might detect vulnerabilities and misconfigurations on individual devices rather than across entire networks, and can be used to help reduce the risk of security threats.
There are different ways to classify types of vulnerability scanners that can be used in each of these scans. Some of these classifications include open-source scanners, network-based scanners, web application vulnerability scanners, and database vulnerability scanners.
- Open-source vulnerability scanners are popular because they are often free and can be easily customized to meet specific business requirements.
- Network-based vulnerability scanners detect network vulnerabilities by scanning ports and services.
- Web application vulnerability scanners are used to detect web application security weaknesses.
- Database vulnerability scanners are used to detect vulnerabilities in databases.
In recent years, cloud-based and online systems have become popular, enabling businesses to use a vulnerability scanner online, rather than installing software themselves. These vulnerability scanners can perform scans on demand, allowing businesses to run quick scans to identify and patch immediate vulnerabilities.
Scanning tools in cybersecurity can be an essential part of vulnerability management, and there are many different types of vulnerability scanning that businesses can use to improve the security of their systems. These types include network vulnerability scanning, host-based vulnerability scanning, and website vulnerability scanning dependent on the intended focus.
Some vulnerability scanners might fall under more than one of these classifications. For example, vulnerability scanners provide a quick and effective way for businesses to identify and address security weaknesses in their systems, and online vulnerability scanners provide businesses with the added convenience of scanning these systems remotely.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
What is Vulnerability Scanning in Cyber Security
In cyber security, vulnerability scanning is a practice of assessing systems, networks, or applications to identify potential security weaknesses or vulnerabilities. This proactive approach to risk management aims to help organizations detect, prioritize, and remediate vulnerabilities before they might be exploited by attackers, using vulnerability scanners. So, what is a vulnerability scanner?
A vulnerability scanner is a software tool that automates the vulnerability scanning process by searching for known vulnerabilities in the targeted system or network. These scanners often leverage a database of known vulnerabilities and attempt to identify those vulnerabilities by simulating attacks. Different vulnerability scanners might focus on different types of devices or security vulnerabilities. These tools also might be available to use online or through the installation and use of client software. So, what is a vulnerability scanner in cyber security? What is its importance?
The benefits of vulnerability scanning in cyber security are numerous. Importantly, the practice helps organizations to reduce the risk of security breaches, data theft, and other security incidents by identifying weaknesses before they can be exploited. It can also be used to help organizations comply with industry regulations and compliance standards.
Other benefits of vulnerability scanning include:
- improved asset management
- detecting outdated software or systems
- prioritizing remediation efforts.
This can be particularly important in large and complex environments where manual vulnerability scanning might be impractical. By automating the process, organizations can scan more frequently and cover a wider range of systems as well as free up human team members for other tasks.
Vulnerability scanning in cyber security is a critical risk management practice that nearly any organization can benefit from. By using vulnerability scanners, organizations can identify vulnerabilities quickly and remediate them before they can be exploited. The benefits of vulnerability, from a cyber security standpoint, include reduced risk of security incidents, regulatory compliance, and more efficient use of human resources.
How Does Vulnerability Scanning Work?
Vulnerability scanning works by utilizing a vulnerability scanner–which is a software tool that automates the process of detecting known vulnerabilities in a network, system, or application. The best vulnerability scanner might be one that can simulate an attack and deliver the most extensive coverage of the network it is scanning.
Some scanners will prioritize and refer to a database of known vulnerabilities, rules, and signatures to determine the possibility of a system being vulnerable. The scanner will then produce a report detailing any vulnerabilities discovered, including recommendations for remediation.
Network vulnerability scanning tools are commonly used for this exercise. These tools enable the scanner to assess network connections and identify vulnerabilities that may be indicative of an attack or weakness that could adversely affect the network’s security.
Vulnerability scanning tools work by following a standard process, typically involving the following steps:
- initiating the scanning process,
- identifying systems to scan,
- scanning the systems,
- detecting vulnerabilities,
- and generating a report.
In more advanced vulnerability scanning tools, the scanner might be capable of scanning for zero-day exploits or new variants of previously known vulnerabilities. The benefits of implementing vulnerability scanning tools include improving asset management, complying with industry standards and regulations, and reducing the risk of cybersecurity attacks.
Regular vulnerability scanning is essential to prevent data breaches, security incidents, and other potential threats to digital systems. Vulnerability scanning can detect weaknesses in existing security systems and provide organizations with the information necessary to patch or otherwise remedy any vulnerabilities.
Vulnerability scanning is an essential tool used in cyber-security to detect vulnerabilities and identify areas of risk. Vulnerability scanner tools are the primary means of achieving this, and network vulnerability scanning tools are a means of achieving network security, specifically. By automating the process of identifying potential vulnerabilities, businesses aim to secure their systems and improve overall data security. The results of vulnerability scanning reports provide actionable items to focus on patching and updating to ensure systems remain secure against emerging threats.
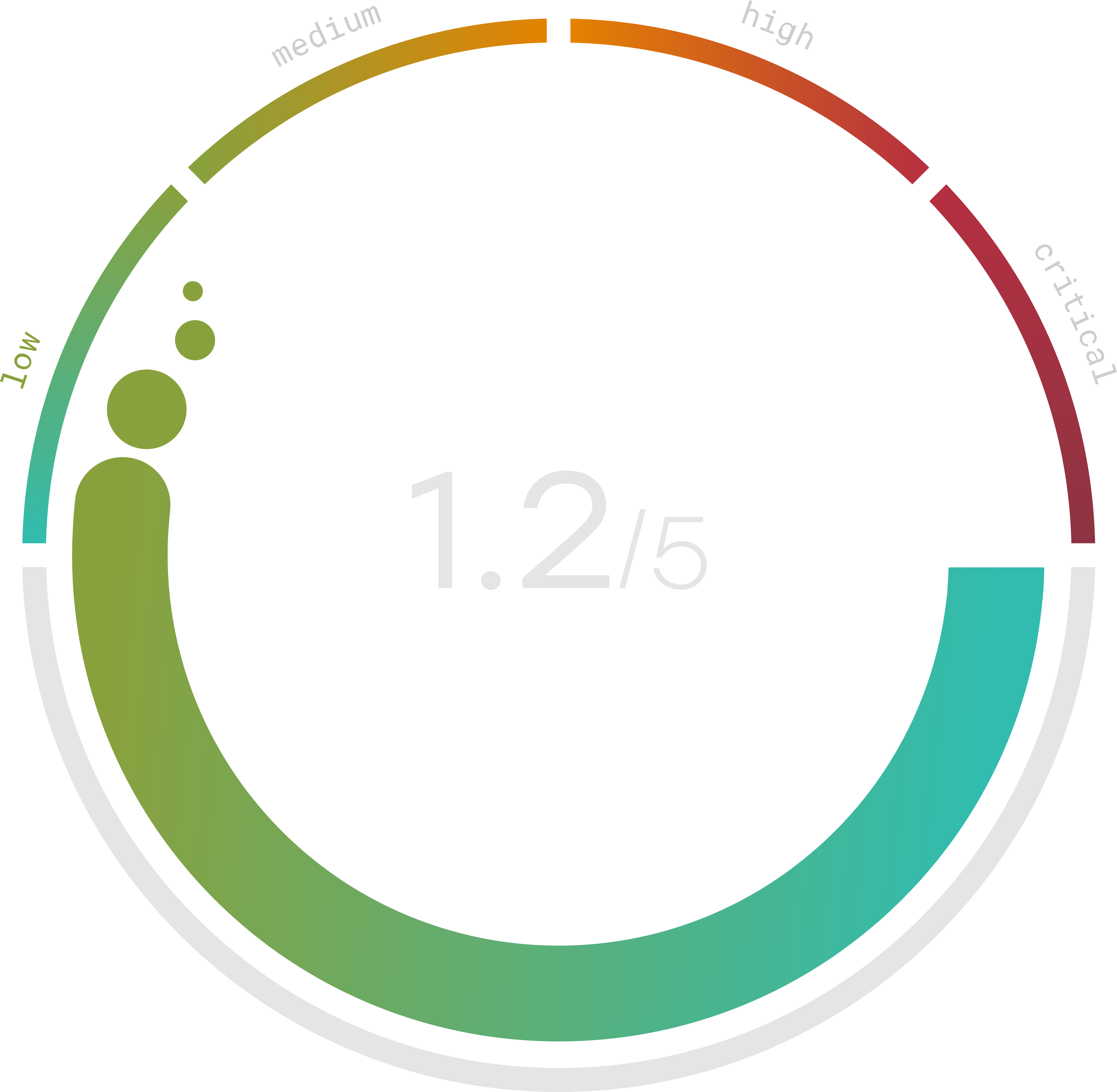
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Vulnerability Scanner Tools
There are many vulnerability scanning tools available, ranging in intended use as well as functionality. For example, one type of vulnerability scanning tool is a website vulnerability scanner. Website vulnerability scanners are often utilized by businesses to identify vulnerabilities on their websites, such as cross-site scripting errors and SQL injection vulnerabilities that attackers may exploit. Website vulnerability scanners can also help protect businesses from denial-of-service (DoS) attacks by locating weaknesses that attackers could use to overload the website’s capacity.
Vulnerability scanner tools are available in both paid and free versions, with differing levels of functionality. Free vulnerability scanning tools are often simple and may not have advanced features like those offered in premium-grade vulnerability scanners. For example, a free vulnerability scanner might be unable to detect sophisticated attacks or advanced malware. For a more robust tool, businesses may opt for paid vulnerability scanning tools.
Database vulnerability scanning tools are also commonly used by businesses and are designed to detect security vulnerabilities in databases. They aim to detect vulnerabilities, such as unauthorized access to confidential information, unpatched software, weak authentication processes, and more.
Host-based vulnerability scanners allow businesses to scan individual devices such as servers, network devices, or workstations, for security vulnerabilities. These scanners can scan individual device systems for vulnerabilities and misconfiguration in order to help reduce the risk of security threats.
Vulnerability scanning tools are a critical part of cybersecurity. Many businesses deploy them to ensure that their networks, websites, and databases remain secure. Network vulnerability scanning tools, website vulnerability scanners, free and paid vulnerability scanner tools, database vulnerability scanning tools, and host-based vulnerability scanners are some examples of tools businesses can utilize to detect and remediate vulnerabilities.
The selection of a scanner might depend on the specific needs of the organization as well as its IT infrastructure. Businesses must be proactive and regularly scan their systems and devices to maintain data security and prevent data breaches.
Vulnerability Scanning Tools Open Source
The best open-source vulnerability scanner might be one that has the capability of performing multiple scans using different databases and techniques, such as signature-based scanning, behavioral analysis, and port scanning.
Examples of some popular open-source scanning tools include OpenVAS, which is a network vulnerability scanner that can be used to identify vulnerabilities in networks, and Metasploit, which is an exploitation framework that can be used to perform penetration testing and vulnerability scanning.
Open-source vulnerability management tools assist organizations in initiating, tracking, and effectively managing remediation processes for detected vulnerabilities. These systems can streamline vulnerability management processes by tracking vulnerabilities, prioritizing them, and presenting data essential for team decision-making.
Another notable benefit of open-source vulnerability scanning tools is the opportunity they can provide for code customization, which allows fast adaptation to change threat landscapes. This flexibility can help businesses better allocate resources and focus on the most severe threats and weaknesses first.
What’s more, open-source solutions have a community support aspect; these tools might be backed up by vast numbers of developers who review and test the software regularly. This can help organizations work to ensure that open-source vulnerability scanning tools remain up to date with emerging threats. Open-source vulnerability scanning tools can be especially useful to businesses where budget constraints might hinder the adoption of proprietary scanning tools.
An open-source vulnerability scanner offers flexibility, customization, and a broad range of capabilities through community support. These open-source vulnerability management tools can provide a streamlined process for the identification, prioritization, and remediation of vulnerabilities in a secure environment, making them a popular choice for businesses looking to improve their cybersecurity practices.
