Sometimes, navigating the complex world of cybersecurity can feel overwhelming, leaving you lost in a maze of terminology and best practices. How can you know where to start? Fortunately, there are standards like ISO 27001. These standards provide a roadmap, enabling you to get the big picture and set your organization on the path to success.
ISO 27001 is an internationally recognized information security management systems (ISMS) standard. It outlines the requirements for an ISMS and provides a framework for establishing, implementing, maintaining, and improving information security. The goal is to ensure organizations have appropriate security measures to protect their information.
The backbone of this standard is the list of controls. Cybersecurity controls are the specific methods by which an organization prevents, detects, and responds to security breaches. The form a particular control takes can vary widely from policies regarding user passwords to the advanced software and hardware used to protect your network from malicious actors. ISO 27001 contains many controls that enable your organization to strengthen its security posture.
This is a broad standard covering an entire ISMS. Because of this, achieving certification can be costly. The full ISO 27001 certification cost varies depending on the size and complexity of the organization. Larger businesses may have hundreds or even thousands of threat vectors and security risks that will need to be mitigated. Generally, certification will include an audit of the organization’s security measures and procedures and a review of the organization’s ISMS. You may also need to purchase additional security measures to meet the standard’s requirements. It is important to note that certification is not an end-all solution and should be used as part of an ongoing security strategy. Also, a certification audit can only be done by a qualified ISO 27001 auditor who has successfully attended the class and passed the ISO 27001 certification exam.
The ISO 27001 standard is available as a PDF document on the International Organization for Standardization (ISO) website. It can be found by simply searching for “ISO 27001 PDF”. This 30-page standard contains the complete list of all the requirements that must be met to achieve certification. These requirements cover topics such as risk assessment, access control, information security policies, incident management, and physical security. By carefully reviewing the requirements and implementing them, your organization can increase its security and achieve compliance with one of the most highly respected international standards.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
ISO 27001 Framework
In the field of construction, a “framework” is a sub-structure that is built to support and uphold a building, wall, or any other larger structure. In cybersecurity, a “framework” is a collection of policies and procedures that also provide a foundation and support to a larger security program. By building your security strategy in line with a recognized framework, you can ensure that you are following best practices and get more peace of mind.
ISO 27001 provides a comprehensive framework for the management of information security and the implementation of security controls. The framework is divided into 14 control categories, each of which contains a series of requirements and objectives that must be met in order to achieve certification. The overall goal of the ISO 27001 framework can be summarized by the three most important categories of information security:
- Confidentiality: only authorized users have access
- Integrity: only authorized users have modification privileges
- Availability: information is always available whenever authorized users have need of it
Each of the controls listed in the framework is focused on achieving one or more of these goals. As part of the standard, it is possible to download the ISO 27001 Framework PDF from the ISO website.
ISO 27001 Controls List
What are the ISO 27001 Annex A 114 controls? These 114 different controls comprise the ISO 27001 Annex A controls list, which every organization must implement in order to achieve certification. The ISO 27001 controls and objectives are divided into 14 domains, each of which covers a particular aspect of information security.
- Information Security Policies
- Organization of Information Security
- Human Resource Security
- Asset Management
- Access Control
- Cryptography
- Physical and Environmental Security
- Operations Security
- Communications Security
- System Acquisition, Development, & Maintenance
- Supplier Relationships
- Information Security Incident Management
- Information Security Aspects of Business Continuity Management
- Compliance
To explore the ISO 27001 clauses and controls list in more detail, we have summarized the first five domains and given examples of the controls, goals, and objectives of each of them.
1. Information Security Policies
In this first domain, the ISO 27001 standard includes controls that require your organization to create and appropriately disseminate information security policies. You will need to have an explicit process for approving and publishing policies, as well as a plan for reviewing the performance of your policies at specific intervals.
2. Organization of Information Security
Good security policies are not enough for compliance or effective security. These policies must also be implemented. In this section, you’ll find controls that are designed to ensure that your organization has clearly defined security roles and responsibilities. Do you have remote employees? How do they fit into your organization’s information security program? These are examples of the kinds of ISO 27001 audit checklist questions you can expect. Your plan for information security needs to be comprehensive and realistic for your entire organization.
3. Human Resource Security
The controls in this section of the standard are focused on employees during their entire lifecycle at the company, from hiring to departure. Here, you will need to have clear policies and processes which ensure that new hires are properly vetted and that existing employees receive adequate security training. You will also need to have policies in place to ensure that departed employees no longer have access to your information systems.
4. Asset Management
Assets include anything that is valuable to your organization. This includes your information and the devices that store it. In order to be ISO 27001 certified, you will need to carefully identify every single asset you have and classify them according to their importance. You will then need to create and maintain processes for ensuring the security of these assets.
5. Access Control
Access control is one of the largest sections in ISO 27001’s list of controls. The controls within this domain are primarily focused on maintaining the confidentiality and integrity of your information systems. Here, you will need to have policies regarding the complexity of passwords as well as the timeframe for changing them. You will also want to have a process for regularly reviewing the access rights of users to ensure that they only have access to the information they need based on their responsibilities.
As you can see, each of the ISO 27001 domains and controls covers a specific aspect of information security. Auditors will methodically move through each domain and compare your organization’s security posture to these requirements in order to determine if you can be certified according to the ISO 27001 standard.
To provide additional guidance about each of the controls within the ISO 27001 framework, the ISO has also provided the ISO 27002 Controls List. This is a guide that supplements the ISO 27001 standard and provides detailed information about these controls.
Businesses should regularly review the controls list to ensure that they are up-to-date with the latest version of the standard. An ISO 27001 certification is technically valid for three years. However, each year the ISO updates the standard to reflect best practices and continually evolving technological capabilities. By staying abreast of these updates, you can ensure that your organization is always ready for any audits and remains protected from the latest threats.
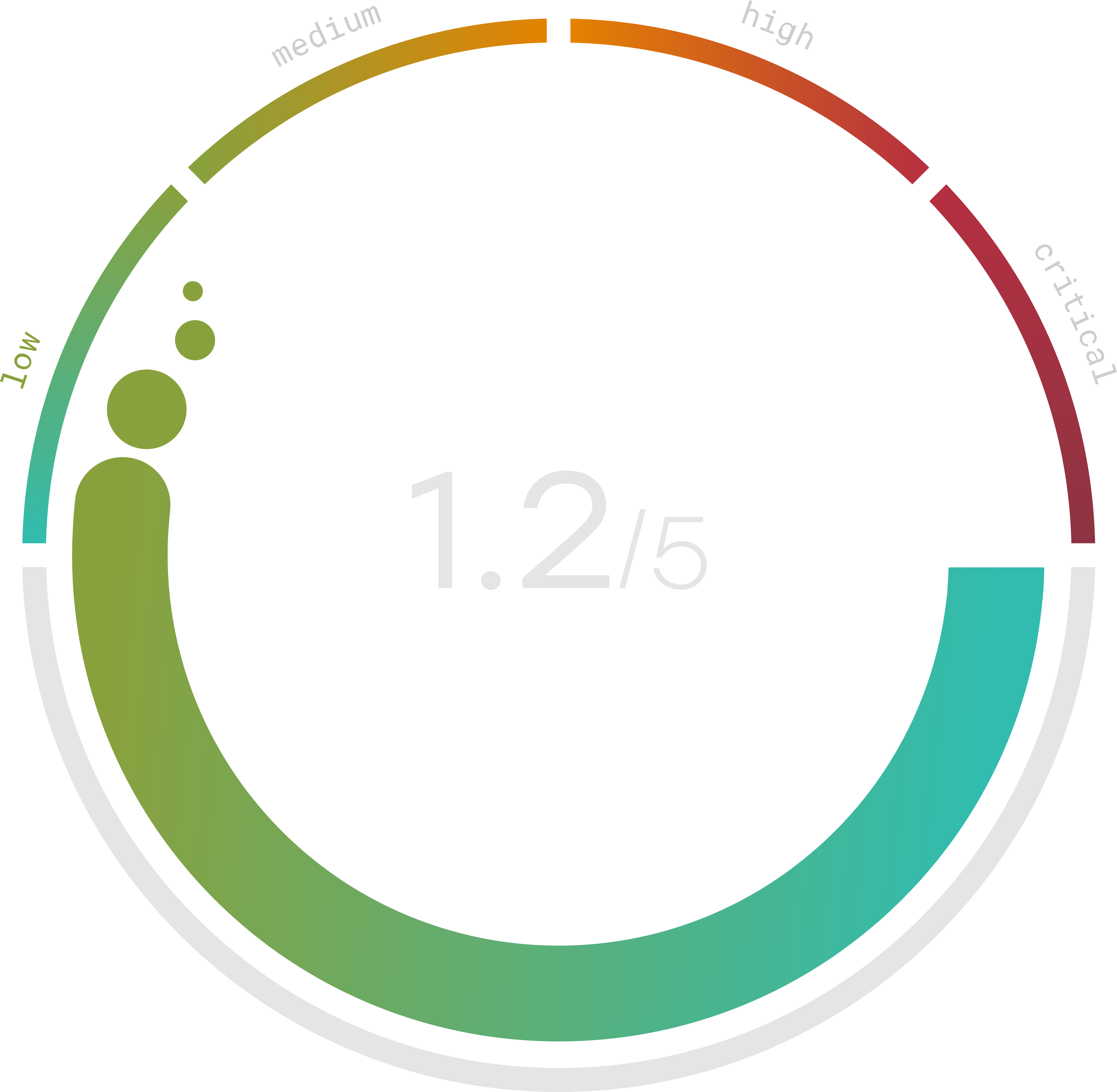
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
ISO 27001 Checklist
Because of the broad nature of ISO 27001, it can be difficult to know where to start. If you are interested in achieving ISO 27001 compliance on your own, the first step is to find and utilize an ISO 27001 checklist. Many of these checklists are available online and can be found by simply searching using a term like “ISO 27001 checklist PDF” or “ISO 27001 Requirements Checklist.” Sometimes, you may also find a checklist in the Microsoft Excel spreadsheet format by searching for “ISO 27001 checklist xls.” However, be sure to rely only on a list that thoroughly breaks down each section and is completely consistent with the overall standard. Having a set list of steps along with a timeline for implementation can reduce the complexity of achieving ISO 27001 certification.
Once you have identified the checklist you want to use, you can then start completing each task. As you go, you will be increasing the security of your organization and steadily becoming more and more compliant with the requirements of the ISO 27001 standard. Having this checklist enables you to track your progress as you get closer and closer to certification. Once you have completed the checklist, your organization will be ready for the audit.
ISO 27001 Controls Checklist
A controls checklist is another list of tasks that can be helpful for any organization looking to achieve certification. More specific than an overall ISO 27001 checklist, an ISO 27001 controls checklist breaks down the 14 domains and specifically lists all 114 different Annex A controls as found in the standard. Along with each control, there should be a description of what it is and how your organization can implement it. Ideally, this checklist would also have a timeline attached so that you could plan exactly when and how each control would be implemented. Overall, a checklist like this can be another powerful tool to push your organization toward compliance and certification with ISO 27001.
Successfully passing the ISO 27001 audit can be expensive, time-consuming, and overwhelming for businesses of all different sizes. If you are looking at ISO 27001 and wondering where to begin, you’re not alone. That’s why we created the Trava Security platform and the Trava vCISO. Our software and services are designed for customization and can be tailored to suit your specific needs. Experience the difference Trava can make for your organization’s cybersecurity by scheduling a demo today.
