Internal scanning is a cybersecurity measure that identifies vulnerabilities within an organization’s internal network. It’s basically a first line of defense against potential cyber threats. Credentialed vulnerability scans go a step further by using login credentials to access network devices and servers. This allows for a deeper, more comprehensive analysis of the system’s security posture, uncovering vulnerabilities that might be hidden from a basic scan. Together, these scans form a robust approach to securing an organization’s digital assets.
Cybersecurity today is a critical business necessity. This is particularly true for the insurance sector, which deals with sensitive client data daily. A single cyber breach can result in significant financial loss and erode client trust. That makes cybersecurity an integral part of risk management for insurance companies.
For insurance agents, mastering cybersecurity measures such as internal and credentialed vulnerability scans is crucial. Credentialed scan cyber security measures serve as a frontline defense in safeguarding client data. Without strong security measures, you run the risk of serious financial loss and damage to your organization’s reputation, which you need for long-term business relationships.
The Significance of Cybersecurity in Insurance
Cyber threats in the insurance industry aren’t just a technical issue but a concern that can damage your entire operation. Cyberattacks cause substantial financial losses each year, from the immediate costs of addressing the breach to the long-term loss of revenue because you’ve lost your clients’ trust. For insurance agents and agencies, maintaining a secure digital environment is an absolute necessity.
The insurance sector is data-centric, dealing with sensitive information like personal identification, medical records, and financial data. A single data breach can have a ripple effect, not just causing financial damage but also severely undermining the trust clients have in their insurance provider. Rebuilding this trust is a long and arduous process, often requiring significant time and resources.
Compliance with cybersecurity regulations is another pressing concern. Regulatory bodies are increasingly stringent about data protection, and failure to comply can result in hefty fines and legal action. Beyond the legal ramifications, there’s an ethical obligation to protect client data. Non-compliance not only risks financial and legal repercussions but also poses a significant ethical dilemma, questioning the integrity of the insurance agency itself.
An Overview of Internal Scanning
What is vulnerability scanning in cybersecurity? Internal scanning is a cybersecurity practice focusing on identifying vulnerabilities within an organization’s internal network. The primary objectives are to prevent unauthorized access and mitigate the risk of data breaches. It’s an effective diagnostic tool, scanning the internal infrastructure to detect weak points that could be exploited by cybercriminals.
For insurance agents, internal scans are an important part of a comprehensive cybersecurity strategy. By identifying vulnerabilities like outdated software, insecure configurations, or unprotected access points, agents can take immediate corrective action. This proactive approach allows them to fortify their network defenses, safeguarding sensitive client data and ensuring the integrity of their digital operations.
In May 2023, Medicaid managed-care non-profit CareSource faced a significant data breach affecting one of its software vendors, MOVEit. The breach led to a $9.9 million lawsuit filed in September, accusing the Ohio-based insurer of inadequate cybersecurity measures that compromised the personal data of over three million customers. The lawsuit alleges that CareSource violated health privacy laws and failed to adhere to industry cybersecurity standards. This case serves as a stark reminder to insurance agents about the critical importance of robust cybersecurity measures, including regular internal scans, to protect sensitive client information.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Diving into Credentialed Scanning
What does a credentialed scan do? What would you use credentials for in a vulnerability scanner? Credentialed scanning is an advanced form of vulnerability assessment that uses login credentials to gain authorized access to network devices and servers. Unlike basic and non-credentialed scans, credentialed scans can delve deeper into system configurations, installed applications, and even specific data files. This provides a comprehensive view of the system’s entire security posture.
For insurance agents, the stakes are incredibly high when it comes to protecting client data. Credentialed scanning offers a more thorough analysis of the network’s vulnerabilities, ensuring that sensitive client data is securely stored and transmitted. It allows agents to identify and rectify potential security loopholes before they can be exploited.
Insurance agents handle sensitive information like personal identification and financial records on a daily basis, Credentialed scans offer a way to go beyond surface-level security assessments. They provide a more comprehensive view of potential vulnerabilities, enabling agents to take proactive measures to secure their digital environment. This safeguards client data and bolsters the agency’s reputation for being trustworthy and reliable.
Benefits of Implementing Internal and Credentialed Scanning for Insurance Agents
1. Safeguarding Client’s Sensitive Information:
-
- Proactively identify and address vulnerabilities.
- Crucial for protecting sensitive information like medical records and financial details.
2. Ensuring Continuous and Secure Business Operations:
-
- Serve as a preventive measure against potential cyber threats.
- Identify vulnerabilities before they can be exploited to ensure smooth operations.
3. Enhancing Client Trust and Business Reputation:
-
- A proactive approach to cybersecurity enhances client trust.
- Secure client information to elevate the business’s overall reputation.
4. Complying with Regulatory and Legal Obligations:
-
- Essential for staying compliant with data protection laws.
- Avoid legal complications and fines by maintaining up-to-date scans.
Implementing internal and credentialed scanning offers a multi-faceted advantage for insurance agents. It secures sensitive client data, ensures smooth operations, enhances client trust, and helps in legal compliance.
Challenges and Solutions
One of the most common challenges in implementing scanning protocols is the lack of expertise and resources, especially for small to medium-sized insurance agencies. The technical complexity involved in setting up and maintaining these scans can be daunting. Without dedicated IT staff, it can seem impossible.
For agencies with tight budgets, outsourcing to cybersecurity experts can be a viable solution. Many third-party services specialize in providing comprehensive scanning solutions tailored to the specific needs of the insurance sector. This alleviates the burden on internal resources but also ensures that the scans are conducted by experts who are up-to-date with the latest cybersecurity threats and solutions.
Adopting a proactive approach to cybersecurity can make a world of difference. Being proactive means implementing security measures before a threat arrives, rather than reacting to a breach after it has occurred.
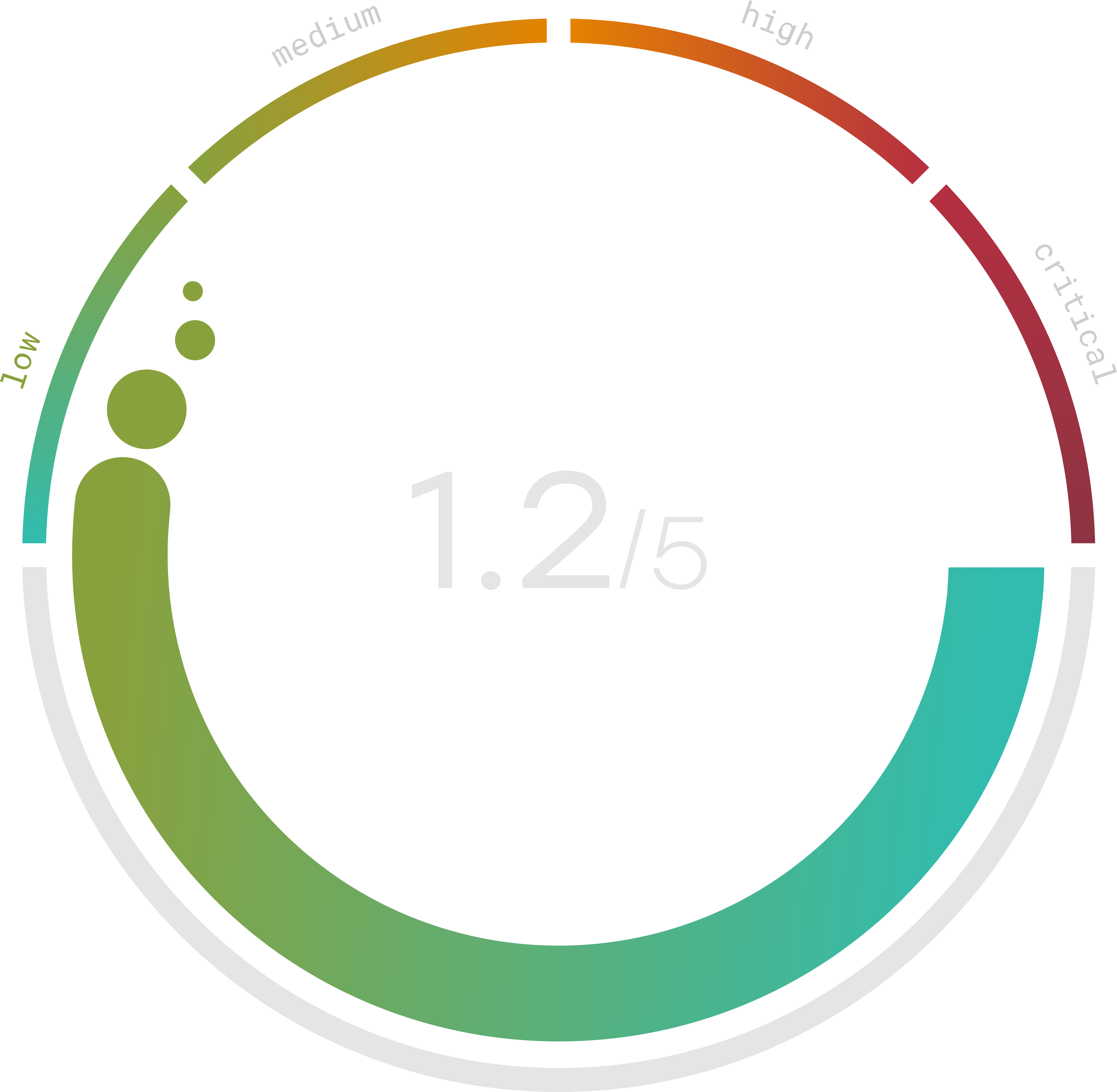
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Case Studies
1. American National Insurance Company: A Vendor’s Vulnerability
- Date of Attack: Undisclosed
- Date Reported: July 7, 2023
American National confirmed a data breach impacting thousands of customers, originating from one of its vendors, Progress Software. The breach exploited the MOVEit vulnerability and compromised various types of customer data, including names, Social Security numbers, and financial account information. A notice revealed that around 35,550 Texans were affected, highlighting the far-reaching impact of vendor vulnerabilities.
2. Sun Life: Third-Party Risks
- Date of Attack: June 2023
Sun Life disclosed a breach affecting its US clients due to a global cyberattack involving MOVEit software. Although Sun Life didn’t use the software, its third-party vendor, Pension Benefit Information (PBI), did. The breach exposed personal data like names, dates of birth, and Social Security numbers. Sun Life stated that no financial or medical data was compromised.
3. Prudential Insurance: The Global Impact of MOVEit Breach
- Date of Attack: May 29-30, 2023
Prudential Insurance also fell victim to the MOVEit data breach, affecting over 320,000 customers. The compromised data included names, addresses, and Social Security numbers. The breach wasn’t discovered until June 27, emphasizing the need for timely detection and response.
Future Trends and Predictions
Cyber threats aren’t static; they evolve continuously, becoming more sophisticated and harder to detect. As a result, cybersecurity measures must also adapt and evolve to counter these emerging threats effectively. The days of set-it-and-forget-it security protocols are long gone.
The insurance sector isn’t immune to these changes. With the advent of Internet of Things (IoT) devices and Artificial Intelligence (AI) in insurance processes, new types of cyber threats are already emerging. These advancements, while beneficial, also create new vulnerabilities that cybercriminals can exploit.
As cyber threats become more complex, the importance of regular scanning and monitoring will only increase. It’s not just about identifying existing vulnerabilities; it’s also about staying ahead of potential future threats. Regular scans will become a cornerstone of any robust cybersecurity strategy, especially for sectors like insurance that handle sensitive data.
Implementing Robust Scanning Protocols
The first step towards robust cybersecurity is forming a dedicated cybersecurity team responsible for implementing and managing scanning protocols. Regular audits should be conducted to assess the effectiveness of these measures and identify areas for improvement. These audits serve as a reality check, ensuring that the implemented protocols are up to the mark.
For insurance agents who may not have the in-house expertise, partnering with cybersecurity experts and solutions providers can be invaluable. These collaborations can equip agents with the specialized vulnerability scanning tools and knowledge they need to protect against evolving cyber threats effectively.
Cybersecurity isn’t a one-time task but an ongoing process that requires continuous evaluation and upgradation. Security protocols should be regularly reviewed and updated to counter new types of threats. This guarantees that the cybersecurity measures in place are always a step ahead of potential vulnerabilities.
Implementing robust scanning protocols involves a multi-pronged approach. From creating a dedicated team and conducting regular audits to partnering with experts and continuously updating security measures, each step contributes to building a fortified cybersecurity framework for insurance agents.
