It is more important than ever to take cyber security seriously. Cyber crime rates are going up every year, costing the United States nearly 7 billion dollars in 2021. The potential risks that come with poor cyber security measures are especially dire for companies that rely on digital devices, applications, and systems. That is where information systems, security, and control can help. Information security controls are countermeasures and safeguards that seek to protect organizations and individuals from security risks.
Some of the most helpful frameworks and guidelines to look at in cyber security PDF are NIST security controls and CIS controls. They go over valuable information such as what the kinds of security controls that you can employ are, what you should prioritize, how you can begin creating an actionable cyber security plan, and how your company is currently doing cyber security-wise. Controls include but are not limited to administrative controls, technical controls, physical controls, and operational controls. Each type of control targets a specific category of informational security needs.
Organizations can use guidelines and frameworks to boost their cyber security effectiveness. They can learn what is the purpose of a privacy impact assessment, among other things. CIS security controls can be used to combat common cyber threats, and the NIST frameworks can help you further mitigate risks.
The size of your organization does not usually matter: cyber security is important. Some sectors are more prone to being attacked by cyber criminals than others. The top target industries for cyber attacks are:
- Business
- Healthcare
- Banking
- Government & Military
- Education
- Energy & Utilities
If you belong to one of these industries, it is important to keep your security measures up to date so that you can be better prepared and protected in the event of a cyber incident.
For organizations that are part of the federal government or associated with it through contracts or otherwise, there are federal information security standards that must be met. These can be quite strict, but compliance is required.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Information Security Controls List
There are numerous types of information security controls that organizations utilize to improve their cyber security. One model that divides security controls into categories has preventive security controls, detective security controls, and corrective security controls as the main categories.
Preventive controls refer to cyber security measures that seek to address weaknesses in your cyber security and prevent risks from penetrating your systems and causing cyber incidents.
Detective controls are meant to detect breach attempts and alert you of data breaches that are in progress. Many types of detective controls exist so that your organization can protect its data from being stolen. The sooner a data breach is detected, the quicker your information security team can act.
Corrective controls, meanwhile, are usually meant to give you more control over your cyber security and systems post-incident. They may work to restore your systems as efficiently as possible so that you can get your operations back on track. They generally focus on minimizing data loss and damages that your information systems have incurred.
A common question people ask is what are the 4 types of security controls that you absolutely need for an organization? This can be answered by looking at the CIS Control V8. When speaking of an information security controls list, people will often refer to the CIS Controls V8 list, which has an updated list of important controls and how you should prioritize them.
The top 4 security controls you might want to consider prioritizing are:
- Inventory of Authorized and Unauthorized Devices
- Inventory of Authorized and Unauthorized Software
- Secure Configuration for Hardware and Software
- Continuous Vulnerability Assessment and Remediation
While different companies may benefit from and prioritize security controls differently, the Controls V8 list can give you a general idea of what is usually most helpful. Some steps may be easier to take than others, such as implementing basic cyber security awareness training or keeping your software updated.
Information Security Controls Examples
There are so many types of controls that it can be daunting to evaluate which ones your organization needs. Popular ones include technical controls, physical security controls, detective security controls, preventive security controls, and administrative security controls. Here are information security controls examples and what you need to know in general about each type.
Administrative security controls examples include separation of duties, data classification, as well as auditing. Many administrative control tools exist to help companies better perform their administrative security functions.
Detective security controls are meant to provide visibility, and they come in the form of logging events meticulously, detecting threat events, and other intrusion detection capabilities. Security tools and platforms can generally help you with important threat detection.
Physical security controls examples are fairly straightforward. You may want to use locks, fences, and alarm systems to prevent outsiders who are not authorized from accessing your systems. Physical security controls can have a high upfront cost.
Technical control examples include antivirus software, anti-malware software, firewalls, and intrusion detection systems (IDS). Technical controls may come in the form of either hardware or software components. Encryption is also a very useful example of technical control security.
Cloud security controls specifically protect systems that use cloud computing to store or transmit data. As more companies become reliant on cloud infrastructure, they also become more vulnerable in ways that are unique to cloud computing. Cloud security controls are ever-evolving and adapting to new cloud-related threats.
The more relevant security controls you use for your organization, the better prepared you will likely be against cyber attacks.
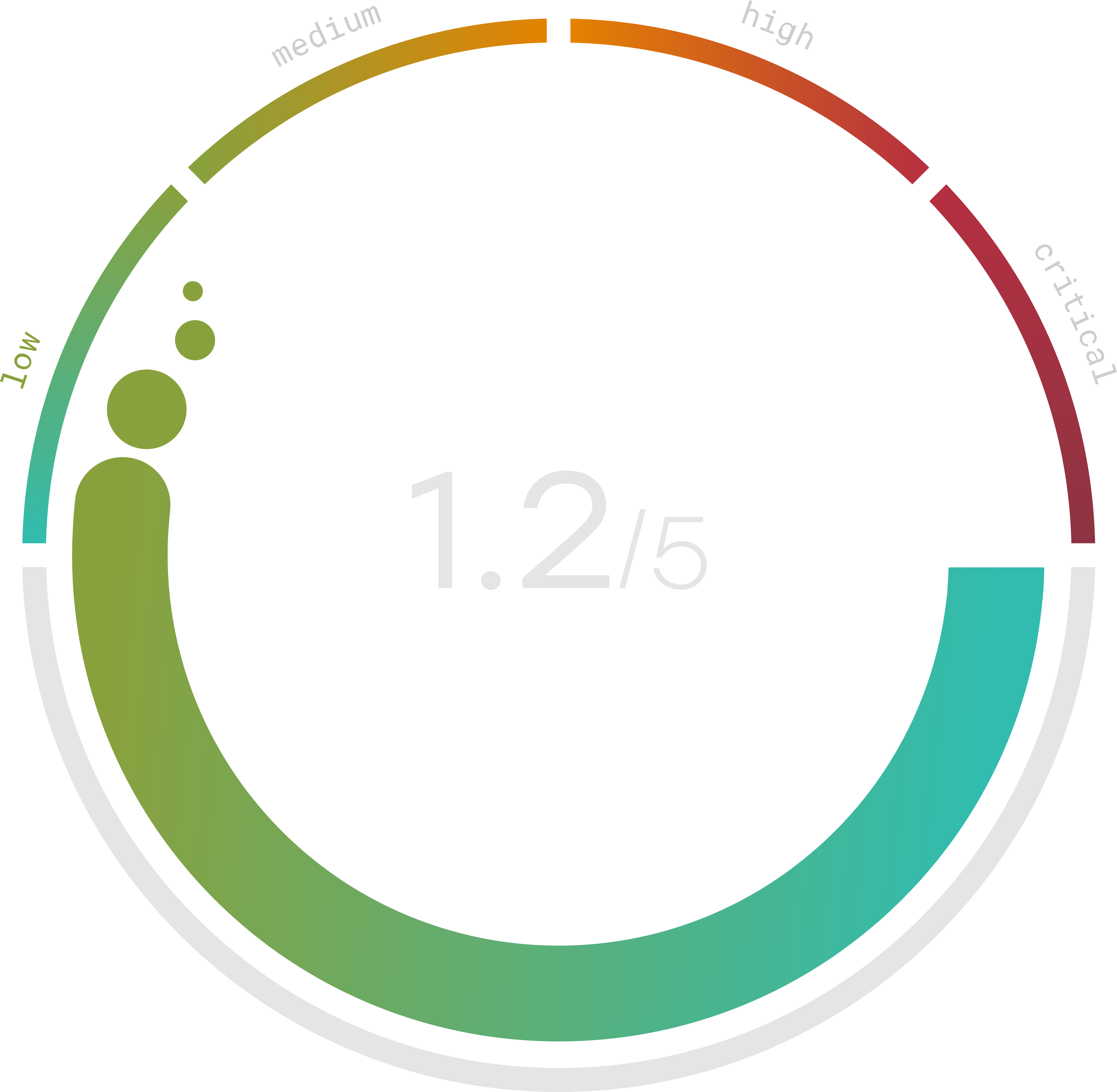
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Federal Information Security Controls Guidance
The Federal Information Security Management Act (FISMA) of 2002 recognized the national importance of cyber security. FISMA compliance is required for all federal agencies, which means that they all have to have adequate information security controls and protections in place. Sensitive information should be protected and there should be minimum baseline controls employed.
For further information, the federal information security controls guidance outlines suggested FISMA-compliant requirements. It is important to achieve the latest FISMA compliance as FISMA is one of the most critical regulations for federal government data protection and standards.
FISMA’s scope has increased substantially since it was first introduced in 2002. It now includes agencies that administer programs such as Medicare, and any private businesses that partake in a contractual relationship with the government must also comply with FISMA guidelines.
FISMA compliance requirements are listed by the National Institute of Standards and Technology (NIST). There are numerous series of key security standards that have been produced and updated over time, including the FIPS 199, FIPS 200, and NIST 800. The top requirements for FISMA compliance are:
- Information System Inventory – Every agency or contractor should keep an inventory of all information systems that are used in the organization. If these information systems have any integrations between each other and other systems in the network, they should be identified.
- System Security Plan – A clear system plan for security should be developed and maintained with regular updates. It should cover security policies, controls, and timetables for implementing new and upcoming controls in the future.
- Risk Categorization – Systems that use sensitive data should be given the highest level of security. There is a range of acceptable risk levels within an organization, depending on the importance of various information systems.
- Security Controls – The NIST 800 outlines an extensive list of security controls that meet FISMA compliance. Not everyone is required to, but the ones relevant to the agency should be implemented.
- Risk Assessments – Agencies should conduct periodic risk assessments that are three-tiered to identify risks across the organization, the business process, as well as the information systems.
- Certification and Accreditation – Agency heads and officials should conduct annual security reviews. These audits can ensure that risks are minimized, and a process with 4 phases for certification and accreditation can be undertaken. They include initiation, planning, certification, accreditation, as well as continuous monitoring.
To maintain FISMA compliance, certain best practices should be followed in general. Companies should stay up to date with new NIST and FISMA standards and guidelines, classify data based on sensitivity levels when created, keep a record of steps taken towards compliance, and encrypt sensitive information (which can be done automatically through the use of tools).
NIST Risk Management Framework
The NIST risk management framework provides a clear process on how you can mitigate and control risk. It can help all sorts of organizations in improving their information security systems against cyber threats and risks.
The NIST 800, also known as the NIST Special Publication 800-53, is a more specific NIST security controls list that goes over security and privacy controls for all U.S. federal information systems. This controls list does not include security and privacy controls that are related to national security.
The NIST 800-53 framework helps organizations that work with or belong to the government comply with mandated FISMA regulations. While the NIST is a non-regulatory agency, it is required that organizations and individual contractors to the government comply with FISMA. The general idea of FISMA and NIST is to keep risks at or below acceptable levels in an efficient, timely, and effective manner.
