Trava is here to provide some information security best practices, standards, and guidelines that will benefit your organization’s security.
Cybersecurity has hit the headlines. A quick google search on “cybersecurity news” delivers about 2,980,000,000 results, and you can find articles on cyber security or even NIST network security in several major newspapers.
With all the talk about cybersecurity, it can be difficult to locate the information you need for your organization—talk about a needle in a haystack! You could download a basics of cybersecurity pdf or dive into NIST network security, but that would only scratch the surface of cyber security.
What you need are more comprehensive cybersecurity guidelines, and we want to provide some information security best practices, standards, and guidelines that will benefit your organization’s security.
Before we get into specific best practices though, we need to establish some general cyber security best practices for business that your organization should be following. Four broad guidelines can help enhance your organization’s cyber security.
First, educate your employees. According to Verizon’s 2022 Data Breach Investigations Report, 82% of security breaches involved a human element. So, all your organization’s employees, not just the IT workers, need to be aware of cyber security—they need to know the common cyber security threats and how to respond to them. This way, everyone can take steps to uphold your organization’s cyber security.
Second, equip your organization with NIST network security. This security, or the National Institute of Standards and Technology (NIST) Framework, is a set of standards that guide organizations in how to protect themselves from cyberattacks. It can help your organization work through five categories of cyber security to ensure that your business is prepared and secure.
Third, protect your sensitive data. Another practical guideline for cyber security is to not put yourself at risk. Loosely secured data is like a sitting duck for hacker threats, so your organization should guard its data carefully. You need to restrict access to sensitive information and use data encryption to protect it from hackers.
Finally, implement IT security guidelines. IT security guidelines can equip your organization’s IT department to handle cyber security threats. Guidelines provide a consistent response that can unite the IT team in threat situations. You might even consider providing different sets of specific guidelines for different cyber security situations.
With these general ideas in mind, you’re now ready to explore the specifics of each security guideline and how they should play out in your organization.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Cyber Security Basics for Beginners
When educating your employees on cyber security, it is good to cover cyber security basics for beginners. You should answer some fundamental questions with your employees to ensure that everyone has a base-level understanding. Here are a few questions to cover.
Why is cyber security? At its most basic level, cyber security is protection against digital crimes. There are many different types of digital crimes, but the most common cyber threats in 2022 that cyber security must protect against include ransomware, phishing, man-in-the-middle attacks, social engineering, and cloud vulnerabilities.
What are the benefits of cyber security? The key benefit to cyber security is that it protects your business from cyber threats. These threats can harm your company operations when they remove customer trust in your business, leak or destroy sensitive information, and/or cost thousands of dollars to repair. So, cyber security is critical to protect against these damages.
Who needs cyber security? You may be tempted to think that only large companies need cyber security and cyber security best practices. But cybersecurity best practices for small businesses are just as important. The CNBC Momentive Q3 Small Business Survey reported that 42% of small businesses have no plan for handling cyber security attacks, which makes them easy targets for hackers. So, all companies should prioritize cyber security.
Those questions give you a good starting place for building your employees’ cyber security awareness with cyber security awareness best practices. Best practices for cyber security are also important for your employees to know though. So, you may consider doing some fun cybersecurity awareness activities to teach them the best practices in handling cyber security threats.
NIST Cybersecurity Framework
For the second cyber security guideline, you will need to use the NIST Cybersecurity Framework, also known as the NIST 800 series or the NIST Privacy Framework, which is a series of documents that enable organizations to guard against cyberattacks. This series is key to helping your organization build NIST network security.
In the NIST Cybersecurity Framework, there are five steps that your organization can follow to establish good cyber security.
The first step is to identify. NIST proposes that your organization should identify the assets they have to protect. The organization also should determine the value of those assets and prioritize protecting the most valuable ones. Additionally, NIST outlines some safeguards that will protect the transport of important assets.
Next, your business should take action to protect its valuable assets. As well as preventing some cyber security threats, this step helps your organization restrict or include the effect of a cybersecurity event.
Third, your organization should work to detect threats. You can monitor your systems and data for any potential cyber security threats and implement mechanisms to detect cyber security incidents as they are occurring.
If a cyberattack does occur, the “respond” step in the NIST Framework helps your organization develop techniques to contain the attack’s impact. Here, speed is essential to limit or even prevent damage.
Finally, your organization needs to recover and return to normal operations after a cyber attack. The “Recover” step outlines some techniques your company can develop to restore any abilities or services that were impaired during a cybersecurity event.
If you are interested in learning more about NIST Cybersecurity Framework, you can look at our blog post on the NIST Framework. Or, if you want to go even deeper into the framework, you can take a course to receive a NIST Cybersecurity Framework Certification from National Initiative for Cybersecurity Careers and Studies (NICCS).
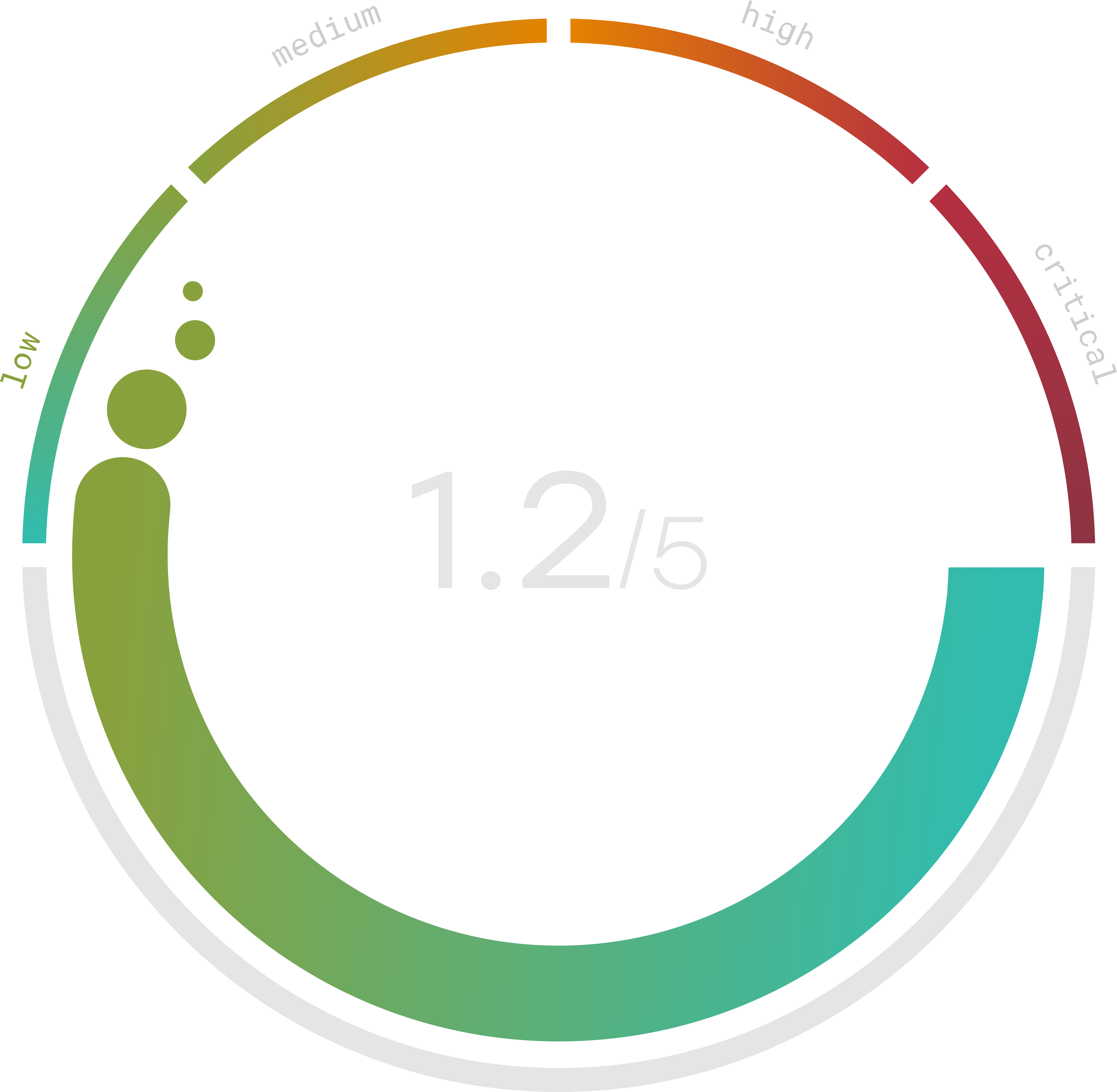
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Data Security Best Practices
For the third cyber security guideline, there are data security best practices you can follow to help protect your data. These are data security best practices for employees just as much as they are for the cyber security team. Remember, everyone needs to play their part to make the cyber security guidelines effective!
First, mark sensitive data. When managing databases, your organization should be sure to mark the sensitive data, which shows them what information to secure. Data discovery and classification technology can help your organization classify and contain the information.
Second, regulate data access and usage. Your organization should control who has access to sensitive information. They can establish a system that only allows certain users to view restricted information. But your organization may also need to have policies on how those privileged users can use the information—which will help prevent careless data leaks.
Third, use physical security best practices. Beyond online security, your organization should also practice physical security to keep its data safe. This can include employees protecting their work laptops from theft, using video surveillance to spot threats, keeping the workplace locked, and clearing a disk drive before recycling it.
Fourth, backup your data. While it may seem like a pain sometimes, your organization should keep encrypted backups of your sensitive company information. These backups can prevent critical data loss if a hacker were to destroy files. They also may help your business during a ransomware attack.
These data security guidelines are some valuable cyber security best practices 2022. 2022 may bring new hackers and more data leaks, but these four tips can help keep your company’s data safe!
IT Security Best Practices Checklist
For the final cyber security guideline, we have an IT security best practices checklist that outlines some security best practices for companies and their IT departments. This checklist is a simple way to help your company enhance its cyber security.
First, set up a firewall. In the event of a cyberattack, the first line of defense will be a firewall, which is a group of programs that prevent outsiders from accessing network data. Per the Federal Communications Commission, this is an essential step for IT cyber security as it can prevent hackers from accessing your company’s systems.
Second, protect mobile devices like phones and smartwatches. Your IT department should make a plan to secure these devices and their connection to the company’s network, and they may need to require employees to password-protect their devices or install security apps.
Finally, your IT department can require multifactor identification for access to the company’s network and important company databases. If hackers determine the password, multifactor identification can still prevent them from accessing the company’s systems.
With this IT network security best practices checklist, you can prepare your company’s IT department to prevent or delay a multitude of cyber threats.
Are you still feeling overwhelmed? Trava specializes in protecting small and midsize businesses from the damage cyber threats can bring. We have many tools available including integrating evaluation and vCISO insights to help you secure your business and establish good cyber security. Schedule a demo with Trava today to see how we can help!
