Cybersecurity is becoming increasingly important for enterprise organizations. Assessing risk can help companies prevent high level cyber threats, data breaches, malware, and more. If you look at small business cybersecurity statistics, you may see that businesses of all sizes and industries are at risk of cybersecurity threats. Even if you think that your business is not large enough to be targeted, you may still have sensitive information that is worth stealing, such as user data. In addition, hackers know that small and medium sized businesses have weaker security measures. These make smaller organizations more vulnerable than larger enterprises.
A cybersecurity assessment checklist or cybersecurity risk assessment matrix can help your organization decide how to mitigate your cyber risks. Tools and procedures can provide you with ways to prepare your company against serious cyber threats. One way to create an easy to understand framework for your organization’s cybersecurity is to utilize a NIST cybersecurity framework PDF or a web application security checklist.
A checklist that acknowledges the NIST Cybersecurity Framework typically looks at the five main ideas of cybersecurity that are listed by NIST. These five are: Identify, Protect, Detect, Respond, and Recover.
The first area, Identify, means that you should make a list of all the equipment and software that you use. This means all of the phones, tablets, computers, and other electronic devices. Data that you use should also be categorized in this list. Next, your cybersecurity team should take measures to create a policy that covers responsibilities for everyone who has access to this data.
Once this has been prepared, it is important to create a protective plan and note down what to do in case a cyber attack goes through and hits your systems. What are the roles and actions of each employee?
The second area is Protect. This is often where companies will use software in order to more effectively protect their data. Sensitive data should be encrypted so that it is safer, and backups of data and systems should be kept in case of catastrophic cyber attacks that can delete all of your information. Simpler but nonetheless important steps of protecting your systems is to update your security software regularly so that you do not risk anything being out of date.
Since human mistakes are a big part of how malware, scams, and other cyber threats can hurt your organization, it is also crucial to train your employees who handle devices with sensitive data. A cybersecurity trainer software or platform can help you sort out how to train your employees.
Next, it is time to Detect. Monitor all of your devices for unauthorized access attempts. Keep track of any USB drives and unidentified software that should not appear in your system. Unusual activities by your employees or on your network should always be investigated.
The fourth area of the NIST Cyber Risk Framework is the Respond. Make sure that your company has a plan in case your data is breached somehow. What will you tell your employees? Your customers? Your sponsors? It is important to have a response and backup plan so that you can keep your operations running as smoothly as possible. Knowing how to report the cyber threat to law enforcement can also help you contain and investigate the attack better.
Finally, it is important to Recover. What will your company do after an attack has occurred? Make sure you know how to repair and restore the various parts of your network that may have been tampered with. Typically, it is a good idea to remain as transparent as you can with your staff and customers about your recovery attempts and activities. If you leave people in the dark, it can worsen the situation immensely.
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Cyber Risk Assessment Tools
Everyone wants to keep their web presence and applications secure, but it is easier said than done. Before you implement software solutions to help improve your cybersecurity, you might want to first assess your cyber risk first. The additional assessments can give you improved insights into what you should spend your security budget on and whether you need to increase the budget for the sake of your business.
Cyber risk assessment tools are one way to monitor risks over time. They can help you identify what your organization needs to improve its cybersecurity quality and how to manage your cyber risk assessment framework.
You might have heard of the NIST cybersecurity framework assessment tool XLS spreadsheets. The NIST is the National Institute of Standards and Technology, which is a part of the U.S. Department of Commerce. It has a special framework called the NIST Cybersecurity Framework, which aims to help organizations of all sizes and types protect their data more efficiently and securely.
Risk assessment tools that are based on the NIST cybersecurity framework tend to focus on five distinct areas: Identify, Protect, Detect, Respond, and Recover. The framework can help you create the best cybersecurity for small businesses and organizations.
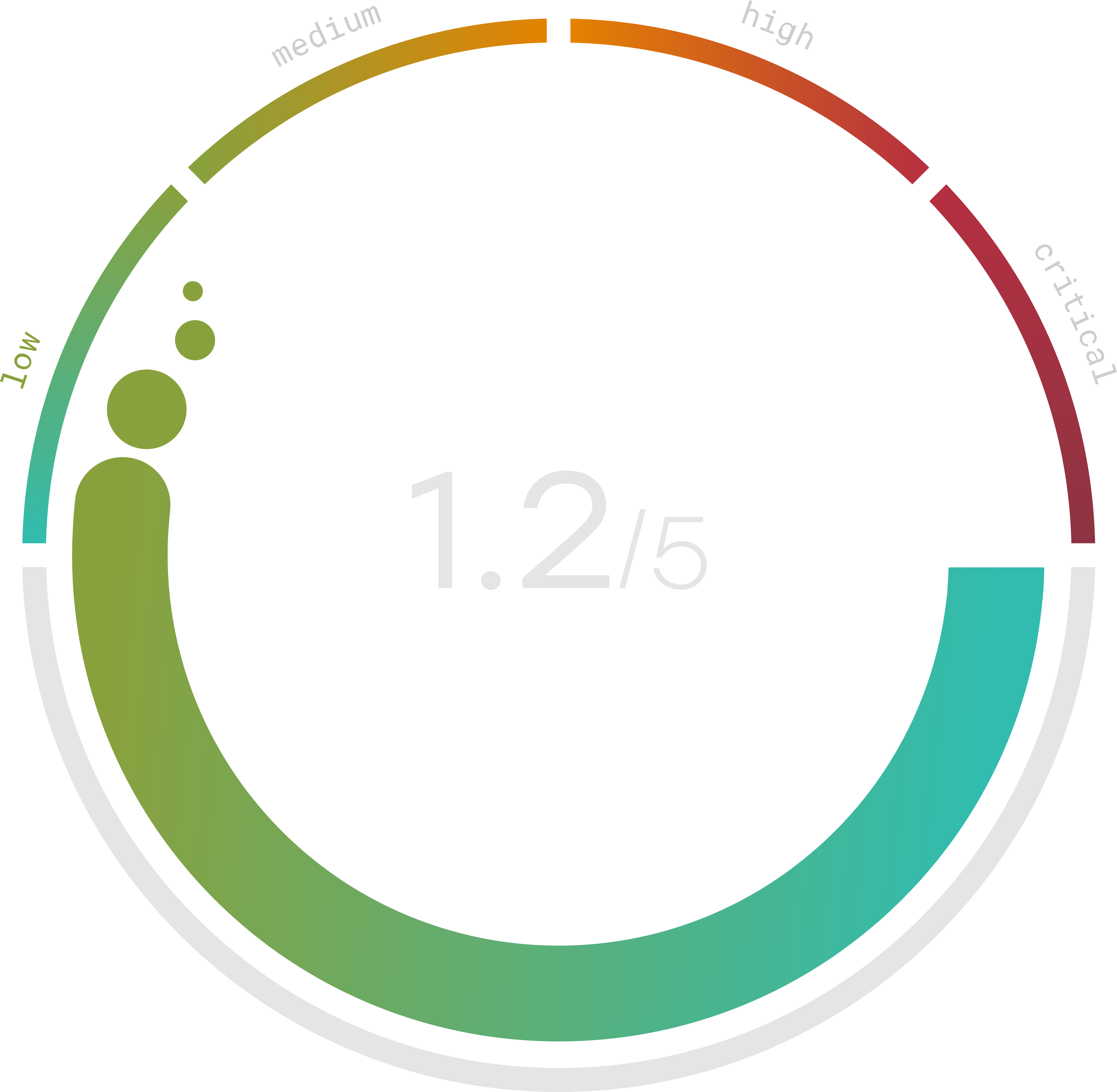
Trava can help you find out what your cyber risk score is at the moment with a thorough cyber risk checkup. This cybersecurity assessment is free and provides you with a vulnerability scan that judges the security of your website. This short assessment can help you better understand your cybersecurity status and what parts of your site are most vulnerable to threats.
Cybersecurity Risk Assessment Template
Cybersecurity can be quite complicated. Sometimes, it is hard to gauge what your particular company needs. If risk assessment is done incorrectly or inadequately, your business may become more prone to attacks or more vulnerable to certain types of cyber risks.
Cyber threats are constantly adapting to the cybersecurity measures that are being developed. A cybersecurity risk assessment template may be able to help you sort out your needs and potential threats. New and dangerous threat actors are emerging frequently, posing risks to plenty of organizations.
When it comes to choosing a cybersecurity risk assessment template, Excel is one of the popular spreadsheet choices. Conducting risk assessment is meant to formally review the risks posed to your particular organization, which includes the threats to your information assets. Potential outcomes can also be mapped out, allowing you to gain more insight into what you need to prepare for.
Another benefit of performing proper risk assessment for cybersecurity is that it can help your business budget for security more effectively. Cyber crimes can be extremely costly. They can cause your critical apps and services to be taken offline, sensitive data to be exposed and stolen, and more. Ransomware and malware are becoming more widely sophisticated and threatening, leaving more businesses attacked on a more frequent basis.
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
Cybersecurity Checklist For Small Business
Cybersecurity for businesses and organizations that are small is just as important, even if it may seem less likely for smaller businesses to be attacked by cyber threats. Cyber threats are prevalent, which means that even startup founders should look over a cybersecurity checklist for small business owners and know what security measures they may need to implement.
A cybersecurity policy for small business PDF will typically show steps that are easier to carry out than a PDF that is meant for a large enterprise. This may be because there are fewer types of risks, which means that a risk assessment might not show as many types of vulnerabilities. However, this does not mean that cybersecurity threats for small businesses cannot be insidious and take down your entire business operations for a long time.
Training your employees with basic cybersecurity knowledge, choosing easy-to-use cybersecurity tools, and performing a cyber risk assessment are all good ways to prepare your small business for potential cyber threats.
Cybersecurity Audit Checklist
While cybersecurity audits can be quite complex, it is critical for your organization’s overall safety. A cybersecurity audit checklist can clarify for you what needs to be done to complete a cybersecurity audit report. If you want to examine what you might be lacking in your cybersecurity measures, you might want to look at a cybersecurity audit checklist PDF. It can help guide you through and understand the NIST audit process.
Many enterprises use NIST as a guideline for auditing security frameworks more effectively. The five areas of the framework – Identify, Protect, Detect, Respond, and Recover – are often present in any cybersecurity risk assessment checklist that you may find online, and for good reason. This framework can help you take action and have a good preparedness plan. Identifying gaps through this assessment is only the beginning. To build a stronger defense and proactively address vulnerabilities, use our Cybersecurity Readiness Checklist.
