While you may be tackling challenges with security and information technology within your company, you may not be compliant with your security needs. Ensuring that your business has compliance security is crucial for your success as an ongoing company, especially one that may be continuing to grow and shift. It is the baseline approach for everything that centers around security efforts and maintenance.
Trava is able to assist you in one key component of business management and cybersecurity: compliance. They, as part of their service, offer opportunities to learn about security compliance and provide tools to ensure you are meeting the goals of compliance. To gather a better understanding of compliance and how it plays into the roles of security and your overall business management, continue reading!
Questions?
We can help! Talk to the Trava Team and see how we can assist you with your cybersecurity needs.
Compliance Security
You may hear the term security compliance thrown around a lot, but what is it? Compliance is the first step to overall security and focuses on the minimum efforts required to establish a secure network for protection. Depending on the organization you are working with, you may have to juggle many different levels of risk management and databases. You must meet the minimum requirements of all of these to meet your security compliance goals. If you do not, it can mean serious consequences for you, your business, and those who interact with your company.
Security compliance examples include laws that all organizations must abide by to ensure client and consumer privacy, such as HIPAA ( Health Insurance Portability and Accountability Act) for those in the medical field. If you work via online platforms, it is also important to make sure you are meeting the minimum standards as well. This is considered cybersecurity compliance. Jobs that require effort include those that must be aware of the mandates in the first place. You must make sure that all employees are aware of these regulations and follow them accordingly.
Depending on the field you are working in, again, you may have different regulations that need to be followed and met in order to establish compliance. Complicity standards are varied and may not be exactly the same across the board, but it is simply a must. Think of it this way, if there was no minimum, there would be zero effort into maintaining security and protection of both personal and professional data that you need to have secured.
What is Compliance?
Compliance, as previously stated, deals with the minimum requirements that must be met in order to ensure the protection of data and sensitive information is in place. It works to specifically ensure that there is a level field that all organizations or businesses of any kind are meeting an exact standard. This plays heavily into fields that share and manage information that is stored via online networks. But what is the relationship in the field of cybersecurity and compliance?
Cybersecurity and compliance go hand and hand with each other, especially in the world of online databases. In the world of cybersecurity, it is important to establish good relationships with these requirements to empower your business to meet compliance requirements and build up a strong framework of IT. Security compliance is extremely important for all businesses. Without this compliance effort, your organization could risk severe troubles down the road including, but not limited to, customer dissatisfaction and distrust, data leaks or attacks, and (perhaps the biggest concern) long-term legal troubles.
The NIST cybersecurity checklist is a great tool. It can work as a cybersecurity checklist for small businesses and larger corporations alike. NIST (the National Institute of Standards and Technology) is the organization that manages and establishes these standards of compliance. Their framework is used to also create resources to help businesses like yours in meeting these standards. If you are interested in learning more about specific standards for your organizational type, you may want to consider investigating their compliance standards or speaking to a representative.
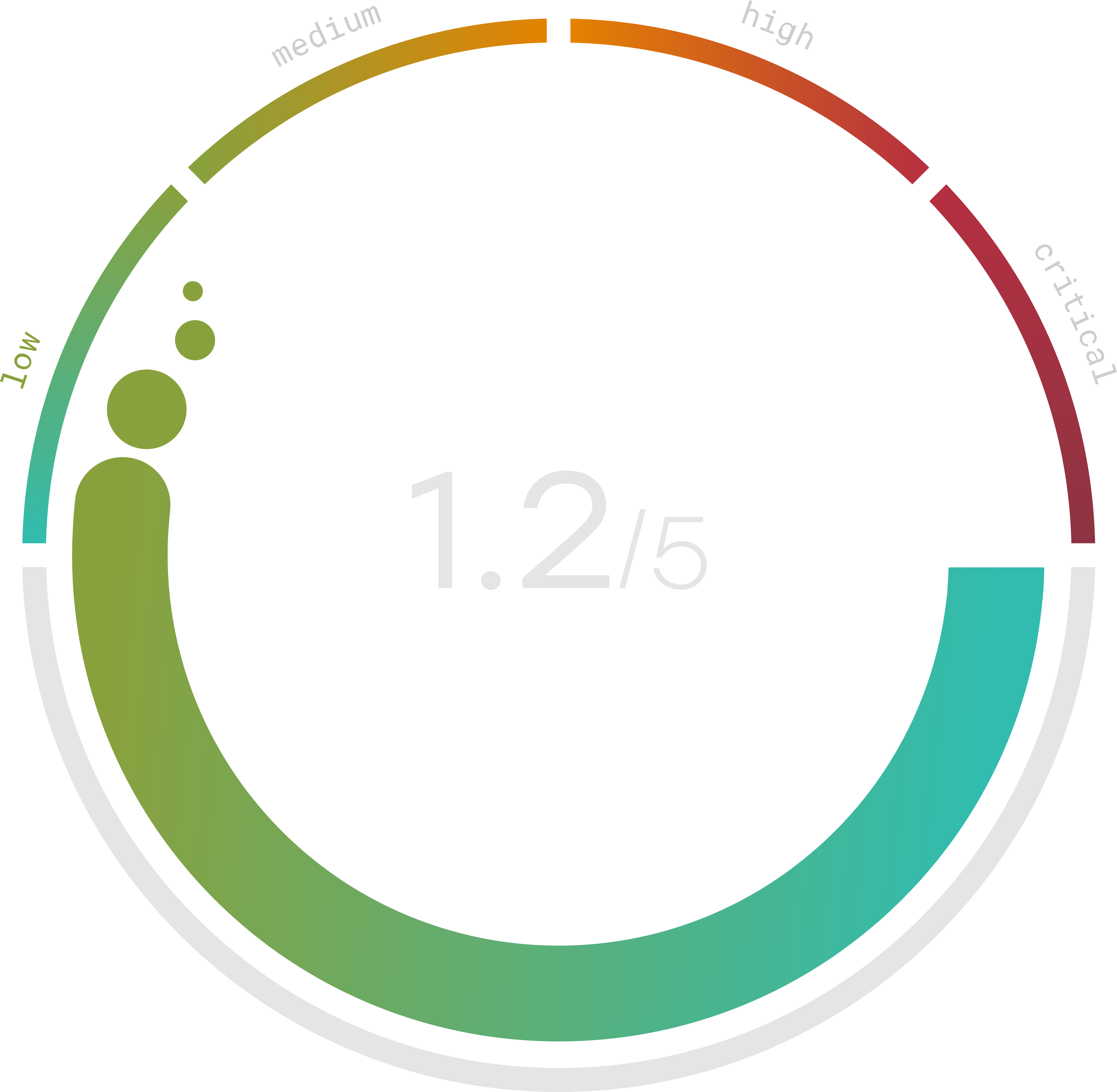
Do you know your Cyber Risk Score?
You can’t protect yourself from risks you don’t know about. Enter your website and receive a completely free risk assessment score along with helpful information delivered instantly to your inbox.
What is Security Compliance Management?
The importance of IT security compliance should not be met with deaf ears or a closed mindset. It can seem like a daunting task to be aware and knowledgeable of all the specific requirements that must be met, even to just meet the minimum requirements, however, it is something that is easily manageable if there is a united effort on the part of everyone in the organization. This falls into the category of security compliance management.
What is security compliance management? Again, it is exactly as it sounds: managing and maintaining a thorough security compliance standards list to ensure that you are either meeting the requirements or exceeding them as a company. The management aspect of this piece is pivotal to the mission of compliance because, while you may say you are committed to these efforts and want to take the proper steps to meet that goal, it can be difficult to achieve compliance without managing these requirements.
Checklists for management are available to make sure you are managing these standards accurately. O information security compliance checklist can be found i. Some of the important standards to note are access and identity control, incident response/disaster recovery, data loss and prevention, and monitoring and reporting. These may already be considerations that you already have, however, it is important to recognize just how important they are in the understanding of security compliance standards. Lists like these provide some insight into the necessary steps you need to take, however, it is up to you and your organization to practice them.
For example, if you do not meet the minimums in data prevention and loss, you have a higher risk of cybersecurity attacks, which can lead to larger dents in your business structure than you may be prepared to handle. Part of that mission can be protected from malware attacks (which is another compliance measure). If you do get attacked or have a massive data breach, it impacts your entire business in a way you may not be able to recover from.
Part of this may be due to gaps in complicity you may not realize you even fall into. These gaps can include:
- Not developing policies in the first place or failing to implement policies.
- Not designating specific employees or groups of employees to maintain and implement the program.
- Permitting the haphazard collection and sharing of PII inconsistent with policy requirements.
- Not updating or modifying policies as the business’s information practices or laws change.
- And several more
Compliance Security Services
Compliance security services are out there and their goal is to help you meet these standards of compliance. For example, AWS (affiliated with Amazon) provides services and resources to assist you in your security compliance mission. The AWS security group offers its own system to meet the requirements of data protection and data prevention loss via its cloud storage system. Cybersecurity compliance services such as this are important because they provide tools, support, and additional resources to assist you in establishing compliance and continuing to manage that compliance long-term.
The AWS security hub has specific resources that can assist you in establishing compliance. One resource they list is a compliance solutions guide that offers quick and easy access to solutions for meeting compliance. This includes a guide on the shared responsibilities model, requesting a compliance report, a security questionnaire, and HIPAA BAA troubleshooting. You can also look into specific case studies about compliance topics so you can put these resources to the test in a secure environment.
Cybersecurity Certifications
You may be thinking to yourself, “wait, there are certifications for cybersecurity compliance?” Why yes, yes there are. The main focus of what we will be touching on are certifications such as SOC 2, ISO, and other certifications in that area. Security compliance certifications such as these show your organization and your consumers your desire to maintain complicity efforts. Security certifications are meant to educate and establish that your organization is aware of complicity standards and has been trained to understand these specific security compliance standards.
Trava has specific tools to assist you in SOC 2, ISO, and HIPAA audits so that you can focus on making sure those standards are being accurately met. This can be beneficial for any organization but can be extremely beneficial for SAAS companies. They do not do the entire process for you, but they do work with you and your organization in order to ensure these complicity standards are being met.
If you are interested in learning more about how Trava can assist you and your security compliance efforts, book a free demo consultation today!
Sources
- https://phoenixnap.com/blog/security-vs-compliance
- https://www.nist.gov/cyberframework/assessment-auditing-resources
- https://prezi.com/d2luxlbfj9ja/introduction-to-nist-cybersecurity-framework-11-old/
- https://www.proofpoint.com/us/threat-reference/it-compliance
- https://aws.amazon.com/compliance/?trk=9bc21f40-12f4-4d2b-8b8d-6f6f65ab19e6&sc_channel=ps&s_kwcid=AL!4422!3!614802967560!e!!g!!amazon%20compliance&ef_id=Cj0KCQjwpeaYBhDXARIsAEzItbGEAUPFpvqq-OW8n2e-dLqvejM1K_rrwj7D2vQVWn8ZopThJ0muXU8aAgbzEALw_wcB:G:s&s_kwcid=AL!4422!3!614802967560!e!!g!!amazon%20compliance
