This blog was updated in July 2025.
Key Takeaways
-
-
Conducting a NIST risk assessment provides a structured way to identify and prioritize cybersecurity risks based on threat likelihood and impact.
-
The five-step process—from identifying threats to calculating risk—helps organizations systematically analyze vulnerabilities.
-
Using NIST’s tools, like the Cyber Risk Scoring (CRS) method, quantifies risk and aids in making informed decisions about mitigation.
-
Real-world examples, such as assessing credit card data theft risks, demonstrate how to apply the framework effectively.
-
Regular risk assessments enable proactive cybersecurity management and support compliance with industry standards.
-
Cyber security matters for businesses, no matter what size. Small- and medium-sized businesses especially can struggle to implement proper cyber security risk assessment frameworks because the task feels too big or too changeable to stay on top of. But bad actors can use this less-than-ideal security to target these smaller, easier-to-infiltrate businesses. That’s where a trusted cyber security team, like Trava, comes in. With just a little outside guidance from the experts, protecting your company’s IT assets can be straightforward.
In this article, we’ll walk you through the basics of carrying out one of the industry standard risk assessments, the NIST risk assessment which is part of the NIST risk assessment framework. This will include:
-
Laying out the 5 steps of risk assessment
-
Exploring what NIST publication is used for risk assessment and where to find it
-
Looking at a NIST risk assessment example
What Are the Steps in a NIST Risk Assessment?
The National Institute of Standards and Technology (NIST) is part of the U.S. Department of Commerce. This institute offers voluntary best practices and a framework for protecting your business from cybersecurity threats. Businesses can use NIST documents to improve their security, but there is no official form to fill out or certification to receive showing your compliance.
A NIST risk assessment framework helps businesses organize and conduct a cybersecurity risk assessment effectively, making it easier to address potential threats and vulnerabilities.
A NIST risk assessment template is useful for recording and organizing the results of a risk assessment using these guidelines.
Several NIST publications deal with risk assessment guidelines, including:
-
NIST Special Publication 800-30: Guide for Conducting Risk Assessments
-
NIST Risk Management Framework 800-37: Risk Management Framework for Information Systems and Organizations; A System Life Cycle Approach for Security and Privacy
-
NIST Risk Management Framework 800-53: Recommended Security Controls for Federal Information Systems and Organizations
A risk assessment is just one part of an overall risk management strategy. There are a variety of approaches recommended by NIST for conducting this assessment, and how it can be integrated into each step of the risk management framework.
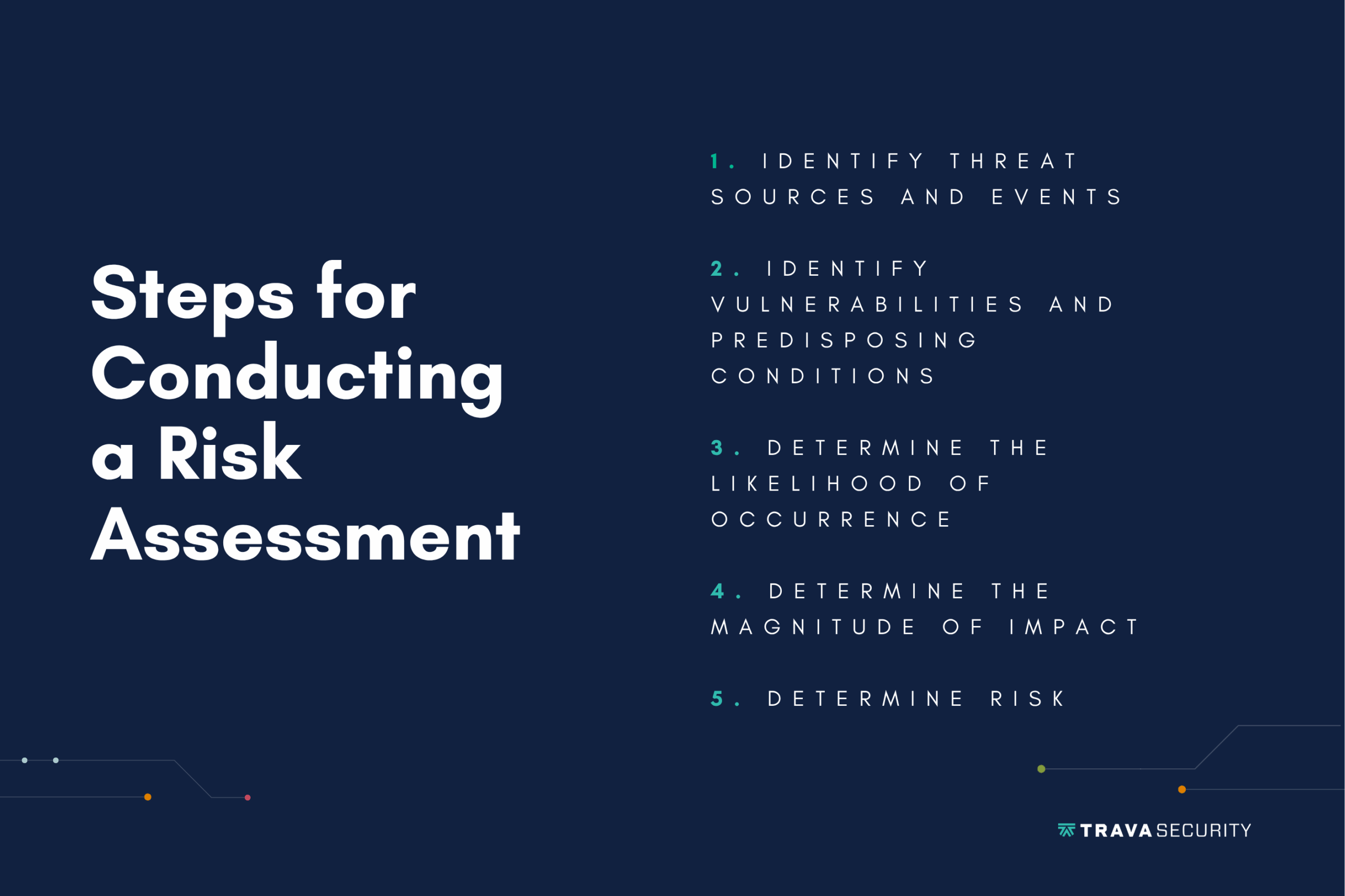
According to NIST 800-30, the basic steps for conducting a risk assessment are:
- Identify Threat Sources and Events
- Identify Vulnerabilities and Predisposing Conditions
- Determine the Likelihood of Occurrence
- Determine the Magnitude of Impact
- Determine Risk
Let’s break down each of these steps into more specific parts, and see how they can be applied within an organization. NIST Special Publication 800-30 gives templated tables for recording each of these steps in the publication appendices when you are ready to carry out your own risk assessment.
1. Identify Sources for Threats
-
Recognize inputs for sources of IT threats. These could include inputs at the level of the organization, the business process, and the information systems.
-
Find input sources of threats for your business. These could include adversarial, accidental, environmental, or structural threats.
-
Decide if threat sources are relevant and significant to your company
-
Make or revise an official record of your decisions. Make sure you include relevant sources of threat and their significance for your organization.
-
For adversarial threats, include an assessment of the bad actor’s capabilities, intent and targeting as it applies to your business.
-
For accidental, structural, or environmental threats, include an assessment of the impact each threat source could have on your organization.
2. Identify Vulnerabilities
-
Recognize the inputs that contribute to your businesses’ vulnerabilities. These could include inputs at the level of the organizational, the business process, and the information systems.
-
Find which inputs contribute to your business’ vulnerabilities.
-
List these vulnerabilities on a record. You may need to create one, or you may be updating an existing document.
-
Assign and record each vulnerability a severity score.
3. Determine the Likelihood of Occurrence
-
Recognize the inputs that influence how likely a cyber security breach is to occur in your organization. Include possible inputs at the organizational, business process, and information systems levels.
-
Find the factors most relevant to occurrence likelihood from documentation in previous steps. This includes things like characteristics of threat sources and vulnerabilities.
-
Determine the likelihood of each threat from both adversarial and non-adversarial events.
-
Assess how likely each threat is to cause significant organizational harm if it were to occur.
-
Compare the likelihood of the threat occurring to how much harm it would cause.
-
Create or update a table to show this comparison.
4. Determine the Magnitude of Impact
-
Recognize the inputs that play a part in determining how much a cyber security breach would affect an organization.
-
Find the factors that apply to your company.
-
Document which impacts would affect which assets.
-
Determine the greatest amount of impact possible on each asset, and record it.
5. Determine Risk
-
Risk is a combination of your organization’s vulnerabilities and the threats it faces. The impacts on your organization by the severity of harm caused by a risk is also relevant.
-
Update all documents following the steps above to create the most complete picture of each variable.
-
Determine risk by combining all these factors into one table that can be easily digested for each risk.
Using a NIST risk scoring matrix at this stage can help organizations visualize the risk severity by mapping likelihood and impact values for each identified threat. This enables businesses to prioritize which risks need immediate action.
Examples of How You Perform a Risk Assessment Procedure
In the NIST Special Publication 800-30, Table I-5 is provided to record the final risk assessment for adversarial risk.
In a hypothetical medium sized software company, this completed chart might look like:
- Threat Event – Customer credit card details stolen
- Threat Sources – Hacker
- Threat Source Characteristics: Capacity – Known previous success
- Threat Source Characteristics: Intent – Access credit card data for making illegal purchases
- Threat Source Characteristics: Targeting – High likelihood, have targeted other similar companies in the same industry recently
- Relevance – High, hackers recently successfully carried out this attack with other companies using the same encryption protection we use.
- Likelihood of Attack Initiation – 80% based on comparison with other similar companies
- Vulnerabilities – Protection we have in place has a weakness vulnerable to these types of attacks
- Severity – High, customers will lose trust in our brand and potential lawsuits for customer financial loss
- Likelihood Initiated Attack Succeeds – 50% based on cyber security assessment results
- Overall likelihood – 40% (and 80% likelihood of an attack with a 50% chance of success)
- Level of Impact – High
- Risk – Very high, addressing this risk should be prioritized
What Is the NIST Cyber Risk Scoring Tool?
Cyber risk scoring is a method for evaluating the strengths and weaknesses in your organization’s cybersecurity approach. It involves assigning a numerical score to each potential vulnerability so you know where to focus your improvement efforts first.
When calculating scores, experts look at factors like:
- The likelihood of a successful attack via that vector
- The potential impact of a successful attack
- The cost of addressing the aftermath of a breach
The NIST Cyber Risk Scoring (CRS) tool is one type of cyber risk scoring. It’s a way to quantify risk based on the NIST cybersecurity framework. You may want to use the tool if you’re seeking NIST certification or preparing for an audit.
The NIST CRS tool revolves around:
- Identifying a security control
- Assigning a weight (from 1 to 10) based on its significance to overall organizational security
- Evaluating the effectiveness of the control
Going through this process for each of your security controls will give you an overall cyber risk score. You can use that number to get a quick snapshot of the threat cybercrime poses to your organization. You’ll also be able to explore the results to find opportunities for improvement faster, as part of your organization’s broader security efforts.
Conducting Risk Assessments is Easy with Trava Security
At Trava Security, we know cyber security can feel like a daunting task. That’s why we provide unique solutions, tailor made for your business. We offer support for:
-
SaaS Leaders – Let us help protect your work, so you can keep doing the innovative work you’re known for.
-
Meeting Compliance Standards – Navigating the complex world of compliance for things like SOC 2, ISO 27001, HIPAA takes time and expertise. Let us do the heavy lifting so your IT staff can focus on making your product better.
Get your free Cyber Risk Checkup to see where you stand now, then contact us to take your cyber security to the next level!
FAQ
What specific NIST publications support risk assessments?
A: NIST SP 800‑30 offers direct guidance for conducting risk assessments. Additional helpful references include SP 800‑37 for the risk‑management framework and SP 800‑53 for recommended security controls.
Do I need to be NIST‑certified to use this framework?
A: No. NIST frameworks are best‑practice guidelines—you can apply their steps without certification. Certification is not required to benefit from the structured approach.
How do I calculate likelihood and impact?
A: Determine likelihood based on threat‑source traits and vulnerabilities. Assess impact severity by considering effects on assets and operations. Report them separately and multiply them (e.g., a matrix) to derive overall risk.
What is the NIST Cyber Risk Scoring (CRS) tool?
A: The CRS tool helps quantify controls and vulnerabilities by assigning weights (1–10) and effectiveness ratings. The result is a numerical score that represents your organization’s cybersecurity posture.
How often should I run a NIST risk assessment?
A: Ideally, conduct assessments:
-
After major changes (new system, process, or compliance requirement)
-
After significant security incidents
-
On a scheduled cadence (e.g., annually or semi‑annually), based on risk appetite and size of your IT environment
Can small and medium-size businesses use this effectively?
A: Absolutely. Trava emphasizes that even SMBs can implement NIST‑based frameworks with manageable effort, breaking the process into clearly defined documentation and risk‑scoring steps.
What’s the difference between risk assessment and risk management?
A: Risk assessment is one phase within broader risk management. It focuses on identifying and analyzing risks. Risk management extends this to implementing, monitoring, and revising mitigations over time. NIST SP 800‑37 details this lifecycle.
Do NIST assessments cover environmental or accidental threats too?
A: Yes. Step 1 includes threat sources such as adversarial actors, accidental errors, environmental conditions, and structural issues. All should be assessed for relevance and impact.


